February 8, 2026
how to get iso 27001 certifiedISO 27001 certificationISMS implementationinformation securitycompliance guide
How to Get ISO 27001 Certified A Practical Guide
Learn how to get ISO 27001 certified with our practical guide. We cover the entire process, from scoping and risk assessment to audits and maintenance.
21 min readAI Gap Analysis
Getting ISO 27001 certified isn't just a technical exercise. It’s a journey that involves building an Information Security Management System (ISMS), performing a real-world risk assessment, putting the right security controls in place, and then proving it all in a multi-stage audit. For most companies, this whole process usually takes somewhere between 6 to 12 months, but the result is a rock-solid security posture and a clear message to the world that you take data protection seriously.
Why ISO 27001 Certification Matters More Than Ever
Before we get into the nuts and bolts of the certification process, let's talk about why this has become so critical. In a world where data is the new oil and cyber threats are a daily headline, just saying you're secure doesn't cut it anymore. You have to prove it. And ISO 27001 is the globally recognized way to do just that.
Getting this certificate is about much more than just satisfying an auditor or slapping a logo on your homepage. It's a strategic business decision that forces a complete shift in how your organization thinks about and handles information security. It weaves security-conscious thinking into the very fabric of your company, from the C-suite to the front lines.
Unlock New Business Opportunities
One of the first things you'll notice is how many doors ISO 27001 can open. It’s simple: big clients, government agencies, and global partners often won't even talk to you without it. It's a non-negotiable requirement. They need to know their data is safe with you and everyone else in their supply chain.
Without certification, you’re often automatically filtered out of high-value RFPs and major contracts, especially in sensitive industries like finance, healthcare, and tech.
ISO 27001 certification is like a universal passport for your business. It tells potential partners anywhere in the world that you've met a tough, internationally respected security standard, removing a huge barrier in sales and procurement conversations.
Holding that certificate means you’re not just making promises; you’re providing proof. That instantly gives you a competitive advantage over others who haven't made the investment.
Build Unshakeable Client Trust
Every business relationship is built on trust. When a customer gives you their data, they’re trusting you to protect it. An ISO 27001 certificate is your proof that their trust is well-placed. It’s independent, third-party validation that you have a working system in place to protect the confidentiality, integrity, and availability of their information. No marketing slogan can ever match that level of assurance.
If you want a deeper dive into the standard itself, check out our comprehensive guide on what is ISO 27001 compliance.
This trust has a direct impact on client loyalty. The next time a competitor suffers a data breach, your certified status becomes a powerful differentiator. It quietly reminds your customers that you've put in the work to manage those very risks.
Fueling the Demand for Certification
The push for ISO 27001 isn't just a passing fad; it's a fundamental market shift. The global market for ISO 27001 certification is on a trajectory to hit an incredible USD 74.56 billion by 2035, growing at a compound annual rate of 15.2%.
What’s driving this? A perfect storm of escalating cyber-attacks and tougher data privacy regulations. This massive growth shows that certification is quickly moving from a "nice-to-have" to a basic cost of doing business.
Laying The Groundwork For Your Certification Journey
So, you've decided ISO 27001 is a strategic move for your business. Excellent. Now it's time to shift from planning to doing. This is where the real work begins, and the decisions you make right now will define the entire project. A successful certification journey starts with one fundamental question: what, exactly, are we certifying?
The first practical step is defining the scope of your Information Security Management System (ISMS). This isn't just bureaucratic box-ticking; it's the single most important decision you'll make. It determines the project's complexity, cost, and timeline by drawing a clear line around what’s "in" and what’s "out."
Defining Your ISMS Scope
Think of your ISMS scope as the walls of your security fortress. What assets are you protecting? Which people, processes, and technologies need to be inside those walls? Your scope statement must clearly outline every component covered by the certification.
For instance, a SaaS company might decide to scope its ISMS to cover only its core product. This would include the development team, the cloud infrastructure where the application is hosted, and the customer support agents who handle sensitive user data. Departments like finance or marketing could be left out for the initial audit, making the first certification much more achievable.
Pro-Tip: Start small and be strategic. It’s almost always better to certify a single, critical product line or location first and then expand the scope in the following years. Trying to certify an entire global operation from the get-go is a recipe for an overwhelmingly complex and expensive project.
The demand for this kind of structured security is surging. We're now seeing approximately 96,000 valid ISO 27001 certificates worldwide, which is a staggering 65% increase from 2021. While IT and digital services still make up about half of these, the health sector is the fastest-growing adopter. It's a clear signal that demonstrating trust is becoming non-negotiable across every industry.
This infographic breaks down the core business drivers that push companies toward certification: building trust, unlocking new markets, and securing a real competitive advantage.
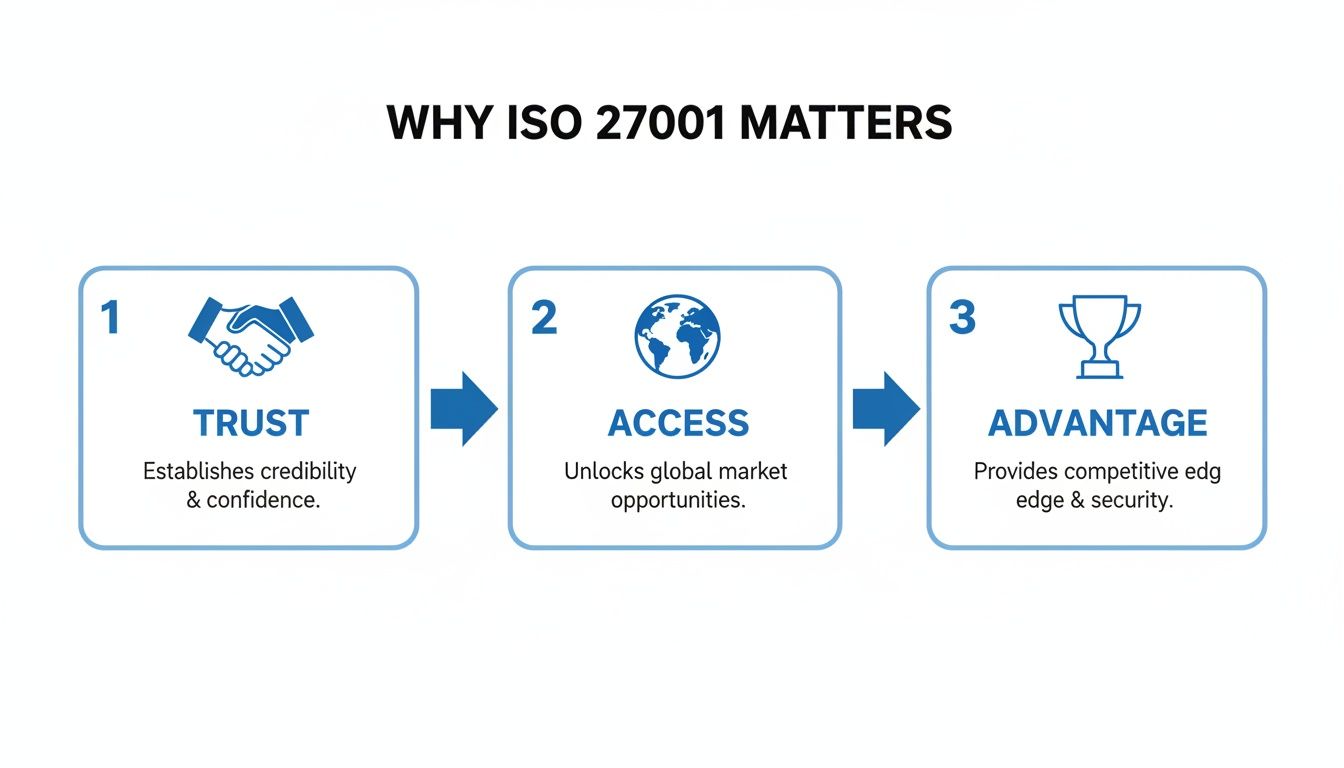
These three pillars—Trust, Access, and Advantage—are what turn an ISO 27001 project from a compliance exercise into a powerful business enabler.
Pinpointing Your Gaps With Precision
Once you’ve locked in your scope, you need a reality check. That’s what a gap analysis is for. This assessment meticulously compares your current security posture against every requirement in the ISO 27001 standard, showing you precisely where you fall short. You can't draw a map to your destination if you don't know your starting point.
Traditionally, this was a painful, manual slog. It meant weeks of interviews, wrestling with massive spreadsheets, and manually digging through hundreds of pages of policy documents. This approach is not only slow but also dangerously prone to human error, which can lead to some very unpleasant surprises during your formal audit.
Thankfully, modern tools have completely changed the game.
AI-powered platforms can now automate this entire discovery phase. Instead of having someone read every policy, you simply upload all your existing documentation—security policies, procedural guides, network diagrams—into the system.
From there, the benefits are immediate:
- Automated Document Analysis: The AI agent reads and understands your documentation, mapping what you already do to the specific ISO 27001 controls.
- Evidence-Linked Reporting: It doesn't just say "you're covered here." It gives you a clear answer with direct citations and deep links to the exact page and paragraph in your documents that serve as evidence.
- Instant Gap Identification: In a matter of hours, you get a comprehensive report that highlights your exact gaps. This lets your team jump straight into fixing problems instead of wasting weeks just trying to find them.
This tech-forward approach doesn't just save a massive amount of time; it gives you a reliable, evidence-backed foundation for your entire ISMS. To dive deeper into this crucial first step, check out our detailed guide on conducting an effective ISO 27001 gap assessment. By using technology smartly, you can compress a task that once took months into a weekend project, dramatically accelerating your path to certification.
Diving into Your ISMS: Risk Assessments and Controls
Now that you've got a handle on your security gaps, it's time to build the engine of your security program: the Information Security Management System (ISMS). This isn't just about creating a stack of documents that collect dust. An ISMS is a living, breathing system designed to actively manage and neutralize information security risks. And it all starts with a brutally honest risk assessment.
This is where the rubber meets the road. A risk assessment systematically identifies, analyzes, and evaluates what could realistically go wrong with your information assets. It’s about putting yourself in an attacker's shoes to find your weak spots before they do.
Uncovering and Analyzing Your Real-World Risks
First things first, you need to figure out what could actually hurt your business. Look past the obvious "hacker breaks into the server" scenario. For most modern companies, especially in tech, the real risks are far more nuanced.
Think about these common situations:
- Cloud Infrastructure Vulnerabilities: What’s the fallout if an engineer misconfigures a critical AWS S3 bucket, leaving it open to the public? The risk isn't just AWS—it's the human error that could leak every piece of customer data you have.
- Third-Party Vendor Dependencies: Your app relies on a third-party API for a core feature. If that vendor gets breached, your customer data could be exposed through no fault of your own. The risk is in your supply chain, not your codebase.
- Insider Threats: It's an uncomfortable truth, but a disgruntled employee with admin access could cause chaos, leak trade secrets, or sabotage systems. This is a human and process risk, not a technical one.
Once you have a list of plausible risks, you need to size them up. This means estimating the likelihood of each risk happening and the potential impact it would have on the business. Scoring each on a simple scale (like 1 to 5) is a great way to prioritize. You can’t fix everything at once, so focus on the threats that are both likely and damaging. We break this down in our complete guide to conducting a cybersecurity risk assessment.
Making Sense of Annex A and the Statement of Applicability
With your risks identified and prioritized, you have to decide how you're going to deal with them. This is where Annex A of the ISO 27001 standard becomes your guide. It provides a menu of 93 potential security controls organized into four distinct themes. Critically, these are not all mandatory.
The four control themes are:
- Organizational Controls (37): The big-picture stuff. Think high-level policies, defined roles, and clear responsibilities.
- People Controls (8): All about the human element, from security awareness training and background screening to secure remote work policies.
- Physical Controls (14): Securing your physical spaces. This covers everything from secure areas and visitor access to a clear desk policy.
- Technological Controls (34): The largest category, covering the technical nuts and bolts like access control, encryption, secure development, and network security.
Your choices get documented in a cornerstone document called the Statement of Applicability (SoA). The SoA is, without a doubt, the master blueprint for your ISMS.
The Statement of Applicability is a non-negotiable for any audit. For every single one of the 93 controls in Annex A, your SoA must clearly state if you've implemented it, explain why (linking it back to a risk you identified), and if you haven't, provide a solid justification for excluding it.
For example, a fully remote company without a physical office can absolutely justify excluding controls for physical site security. That justification is the key—you can't just skip controls you don't feel like doing. The SoA demonstrates to an auditor that your security program is the result of a deliberate, risk-based process.
From Policy on Paper to Hands-On Implementation
With your SoA locked in, the project shifts from planning to doing. This is where your written policies become real, tangible actions that actually make your company more secure.
Your implementation plan will touch nearly every part of the organization.
- Configuring Access Controls: The IT team might start implementing role-based access control (RBAC) in your cloud environment, making sure people only have access to what they absolutely need for their job.
- Launching Employee Training: HR and security could team up to roll out mandatory security awareness training, teaching everyone how to spot phishing emails and who to call when something looks suspicious.
- Refining Incident Response: Your engineering leads will dust off the incident response plan and run a tabletop exercise to make sure everyone knows their role when a real security event happens.
During this phase, good documentation is your best friend. For every control you implement, you need to collect evidence that it's in place and working correctly. This isn’t just about having a policy document; it’s about having proof. Think screenshots of system settings, training completion reports, or meeting minutes from your management reviews. Keeping this evidence organized and tied directly to your SoA will make your audit infinitely smoother.
Navigating Your Internal and Certification Audits
You’ve spent months building your ISMS, and now it’s time to put it to the test. This is where the rubber meets the road—proving that your security program is more than just a stack of documents. The validation process unfolds in two critical phases: your internal audit, followed by the external certification audit.
Think of the internal audit as the final dress rehearsal. Its entire purpose is to find the gaps before an external auditor does. This can't be a quick once-over; it has to be a detailed, objective review of your whole ISMS, and crucially, it must be performed by someone independent of the work they're auditing.
I’ve seen many organizations rush this step, and it’s always a mistake. A proper internal audit gives you a clear, actionable punch list of non-conformities to fix, so you can walk into your certification audit with confidence, not anxiety.
The Two Stages of Your Certification Audit
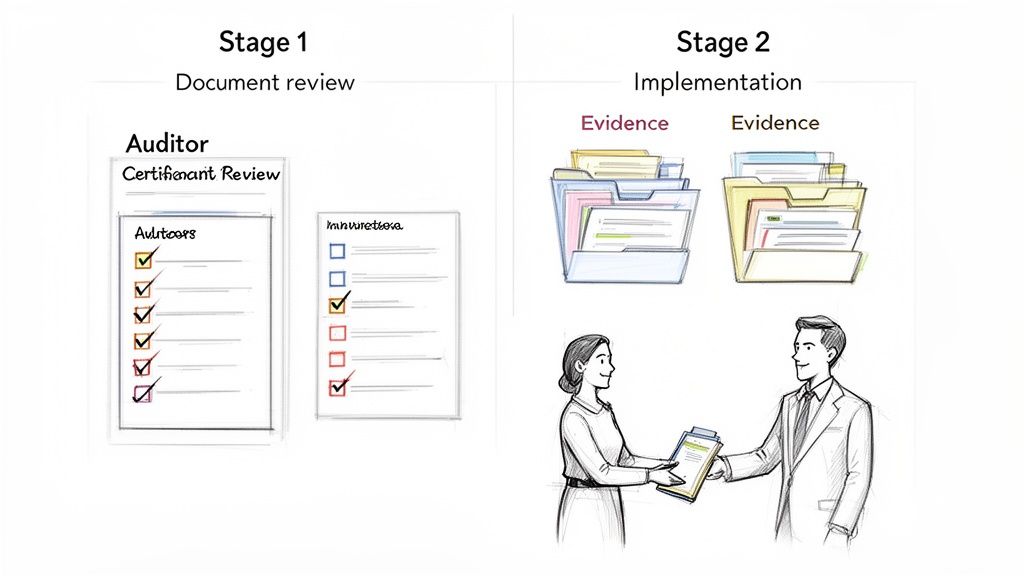
The external audit is the official performance, conducted by an accredited certification body. It’s strategically broken into two parts to ensure your ISMS is not only designed correctly on paper but is also a living, breathing part of your organization.
Stage 1: The Documentation Deep Dive
The first part, known as the Stage 1 audit, is all about the paperwork. The auditor will sit down and meticulously review your core ISMS documentation. They’ll be looking at things like:
- Your ISMS scope statement
- The risk assessment and treatment plan
- Your Statement of Applicability (SoA)
- Key policies and procedures
The goal here is simple: to verify that your documented ISMS meets all the requirements of the ISO 27001 standard. The auditor is essentially checking your homework. A successful Stage 1 ends with a report that might flag a few minor issues but ultimately gives you the green light to proceed to the main event.
Stage 2: Proving It in Practice
The Stage 2 audit is where you have to show, not just tell. The auditor moves beyond the documents to verify that your controls are actually implemented and working as intended. This involves interviewing your team, observing processes, and—most importantly—requesting hard evidence.
This is where all your preparation really pays off. The auditor might turn to a developer and ask, "Show me how you handle a new employee's access request." They won't be satisfied with seeing a policy document. They'll want to see the filled-out access request forms, the system logs proving permissions were granted correctly, and confirmation that this process is followed every single time.
One of the most common reasons for failing an audit is a simple lack of objective evidence. It’s not enough to say you do something; you have to prove it with records, logs, and other artifacts. Poor evidence management is a fast track to getting a non-conformity.
This is exactly why modern compliance platforms are so helpful. Tools that automatically link evidence directly to controls can be a lifesaver. When the auditor throws a tough question your way, you can instantly pull up the precise screenshot, log file, or training record needed, demonstrating absolute command over your ISMS.
To better understand the distinct roles of these two audits, let's break them down side-by-side.
Comparing Stage 1 vs Stage 2 Certification Audits
| Audit Phase | Primary Focus | Auditor's Objective | Common Pitfalls to Avoid |
|---|---|---|---|
| Stage 1 | Documentation Review | To confirm the ISMS design meets the standard's requirements on paper. | Incomplete policies, a poorly defined scope, or an inadequate risk assessment methodology. |
| Stage 2 | Implementation & Effectiveness | To verify that controls are operating as described and are effective in practice. | Lack of objective evidence, inconsistent process execution, or staff being unaware of relevant policies. |
Ultimately, Stage 1 confirms you have a solid plan, while Stage 2 proves that you're actually following it. Passing both is what earns you the certificate.
Setting Yourself Up for Success
The audit process doesn't have to be intimidating. A little bit of foresight goes a long way.
Here are a few common tripwires I see companies stumble over:
- Weak Management Review: Auditors will absolutely ask for the minutes from your management review meetings. If you can't show documented commitment from leadership, that's a major red flag.
- Outdated SoA: Your Statement of Applicability is a living document. It must be a perfect mirror of the controls you have in place at the moment of the audit.
- Skimping on the Internal Audit: I'll say it again—cutting corners on your internal audit is a false economy. It’s your single best opportunity to find and fix problems on your own terms.
The pressure to get this right is only increasing. Recent data shows that 81% of organizations either have or are planning for ISO 27001 certification, a huge jump from 67% just the year before, highlighting its dominance over other security frameworks. This is part of a broader audit culture, where 92% of companies now run at least two security assessments every year. You can discover more insights about this compliance surge and what it signals for the industry at large.
You’ve earned your ISO 27001 certificate. That’s a massive accomplishment, and you should absolutely celebrate it. But don’t make the mistake of thinking you’ve crossed the finish line. In reality, you’ve just started a new, ongoing race.
An ISMS isn't a one-and-done project where you can dust off your hands and walk away. It’s a living, breathing commitment to managing security day-in and day-out. The moment that certificate is issued, a three-year clock starts ticking.
This cycle is designed to make sure your ISMS stays sharp and evolves right alongside your business and the ever-changing threat landscape. This is how you embed security into the very DNA of your operations, turning it from a static pile of documents into a dynamic system that actively protects your organization.
The Three-Year Certification Cycle
Your ISO 27001 certificate is valid for three years. To keep it, you'll have to prove to your certification body that your ISMS is still working effectively through a couple of follow-up audits.
-
Annual Surveillance Audits: These happen in Year 1 and Year 2. Think of them as check-ups. They aren't as exhaustive as the initial certification audit, but they are just as important. The auditor will sample different areas of your ISMS each year to verify that you're maintaining compliance and, crucially, making continuous improvements.
-
Recertification Audit: This is the big one, scheduled for Year 3 right before your current certificate expires. It’s a full-blown reassessment of your entire ISMS, much like the original Stage 2 audit. Passing this renews your certification for another three-year term.
Let's be clear: if you aren't prepared for these audits, you could have your certificate suspended. After all the hard work to get it, that's a blow no one wants to take.
Building a Culture of Continuous Improvement
The key to long-term success is shifting your mindset from "getting certified" to "staying certified." This means security management has to become just another part of how you do business, not a frantic scramble to get ready for the auditor.
A few key activities need to become second nature.
First up is the periodic management review. This isn't just a quick status update; it's a formal, strategic meeting where your leadership team gets in a room and really digs into the ISMS performance. They need to confirm it still aligns with business goals and is effectively managing risk.
An auditor will always ask to see the minutes from your management review meetings. If you can't show documented leadership oversight, that's one of the fastest ways to get hit with a non-conformity.
You also need to establish a steady rhythm of continuous monitoring. This is the day-to-day work of making sure your controls are actually working. It might involve reviewing access logs, running vulnerability scans, or simply checking that employees are up to date on their security awareness training.
How to Handle Non-Conformities and Corrective Actions
Even the most well-oiled ISMS will run into issues. Whether you find it yourself during an internal audit or a surveillance auditor flags it, a non-conformity is just a sign that you've missed a requirement of the standard. It happens. What really matters is how you respond.
When you identify a non-conformity, you need a structured game plan:
- Find the Root Cause: Don't just slap a bandage on the problem. You have to figure out why it happened. Was it a broken process? A gap in training? A technical glitch?
- Create a Corrective Action Plan: Lay out the exact steps you’ll take to fix the root cause and ensure it never happens again.
- Implement and Verify: Put your plan into action. Then, gather evidence to prove that the fix actually worked and the problem is solved for good.
This disciplined approach shows auditors that your ISMS can self-heal and improve. It’s a sign of maturity and a real commitment to the principles of ISO 27001, turning a potential failure into a powerful display of your system's strength.
Your ISO 27001 Questions, Answered
If you're starting to think about ISO 27001 certification, you've probably got a lot of questions about what the process actually looks like in practice. It’s easy to get bogged down in the standard itself, but what most people really want to know is: How long will this take? What's it going to cost? And where do things usually go wrong?
Let's cut through the noise and get straight to the practical answers I share with clients every day.
How Long Does It Take to Get ISO 27001 Certified?
This is always the first question, and the honest answer is: it depends. For most small to medium-sized businesses, you should plan on a 6 to 12-month journey from start to finish. I've seen people try to rush it, and it almost always backfires during the audit.
Think of it in two big chunks. First, you have the implementation phase, which is all the internal work. This is where you’re conducting your risk assessment, writing policies, and actually putting new security controls in place. That typically takes a solid 3-6 months.
The second half is the audit cycle itself, which also takes another 3-6 months. This involves the official Stage 1 and Stage 2 audits with your chosen certification body, plus any time you need to fix issues they might find.
Of course, your company’s size, the complexity of your operations, and your current security maturity will all influence that timeline. A larger enterprise with multiple locations might be looking at a 12 to 18-month project.
Here's a pro tip: the timeline isn't completely out of your control. Strong leadership buy-in, a dedicated internal team, and smart use of automation can seriously speed things up. Using an AI-powered tool for your initial gap analysis, for example, can trim weeks, sometimes even months, off the initial prep work.
What Is the Average Cost of ISO 27001 Certification?
There’s no single price tag for ISO 27001. Instead, you need to budget for a few different things. For a typical small or medium-sized company, a realistic budget is anywhere from $15,000 to $50,000+ for the first three-year certification cycle.
Here’s a rough breakdown of where that money goes:
- Implementation Costs: This is the most unpredictable bucket. It covers any external consultants you hire, the cost of employee training, and any new security tools or software you need to buy to fill the gaps you've identified.
- Audit Fees: Your accredited auditor will charge for the Stage 1 and Stage 2 audits, plus the two annual surveillance audits that follow. These fees alone can easily run from $10,000 to $25,000 over the three years.
- Internal Resources: This is the "hidden" cost that trips up a lot of companies. Don't forget to account for the time your own people—from IT and engineering to HR—will spend on this project. It's a significant investment.
One way to get a better handle on these costs is by using a compliance automation platform. They can dramatically reduce the manual labor your team has to put in and often make it possible to skip the expensive external consultants altogether.
Can We Get Certified Without an External Consultant?
Absolutely. It's becoming more and more common, especially for tech-savvy companies that already have some security expertise in-house. You don't need a consultant to get certified.
What you do need is the right internal setup. To pull this off, you have to have a dedicated project lead who truly owns the process from beginning to end. Just as important, you need clear and visible support from your leadership team to give that person the authority and resources to get the job done.
This is where modern compliance platforms really shine. They're designed to guide your internal team through every step, automating the most painful parts like evidence collection and gap analysis. Not only does this save a ton of money on consulting fees, but it also builds that critical compliance know-how within your own organization for the long run.
What Are the Most Common Audit Failures?
Learning from others' mistakes is the smartest way to prepare for your own audit. After years in this field, I can tell you that auditors tend to find the same problems over and over again.
The number one reason for an audit failure, by a long shot, is a lack of objective evidence. You can talk all day about your amazing security controls, but if you can't show the auditor the logs, records, and reports to prove it, it doesn't count. The auditor’s mantra is simple: "If it's not documented, it didn't happen."
A few other classic pitfalls to watch out for include:
- A shallow or incomplete risk assessment.
- No proof of management commitment (e.g., missing meeting minutes from leadership reviews).
- Inadequate records of employee security awareness training.
And finally, a rookie mistake I see all too often is skipping or rushing the internal audit. Your internal audit is your dress rehearsal. It’s your last, best chance to find and fix problems on your own terms before the external auditor shows up at your door.
Ready to fast-track your path to ISO 27001 certification? AI Gap Analysis transforms weeks of manual work into a few hours of automated, evidence-linked discovery. Upload your documents and let our AI agent pinpoint your gaps with precision, so you can focus on what really matters—building a stronger security posture. Get started today at https://ai-gap-analysis.com.