February 14, 2026
how to prepare for an auditaudit readinesscompliance auditgap analysisaudit evidence
How to Prepare for an Audit A Practical Readiness Guide
Learn how to prepare for an audit with our practical guide. We cover everything from scoping and evidence collection to gap analysis and remediation.
23 min readAI Gap Analysis

An audit on the horizon can feel like a storm gathering, but the secret to navigating it successfully isn't last-minute scrambling—it's methodical preparation. The very first thing you need to do is define a precise scope, then establish a realistic timeline, and finally, assign clear roles to your team. Getting these foundational pieces right from the start turns a chaotic, stressful process into a well-managed project.
Building Your Foundational Audit Roadmap
Audits are becoming more and more common. It's not just a feeling; the numbers back it up. A recent report from A-LIGN found that a staggering 58% of organizations globally went through four or more compliance audits in a single year. For larger companies, that number is often even higher. With regulators turning up the heat, having a solid plan isn't just a good idea—it's a must.
Without a clear roadmap, teams end up spinning their wheels, chasing down evidence that doesn't matter or duplicating work because no one knows who’s doing what. Your roadmap is your single source of truth. It gets everyone on the same page about what needs to be done, who owns it, and when it's due.
Define Your Audit Scope
First things first: you absolutely have to nail down the audit's scope. This means getting crystal clear on which systems, processes, business units, and physical locations are in play. Any ambiguity here will come back to bite you. A fuzzy scope is a recipe for confusion, wasted effort, and a whole lot of frustration.
Let's say you're gearing up for an ISO 27001 audit. Does it cover just your production environment, or are the dev and staging environments included too? Are we talking about all your offices, or just the main headquarters? You need to have concrete answers to these questions before you do anything else. It prevents the dreaded scope creep and ensures your team is focused on what truly matters.
Think of a well-defined scope as your North Star for the entire audit. It keeps the team focused, eliminates nasty surprises down the road, and makes your evidence collection pointed and efficient.
This visual guide breaks down how to put together a solid audit roadmap.
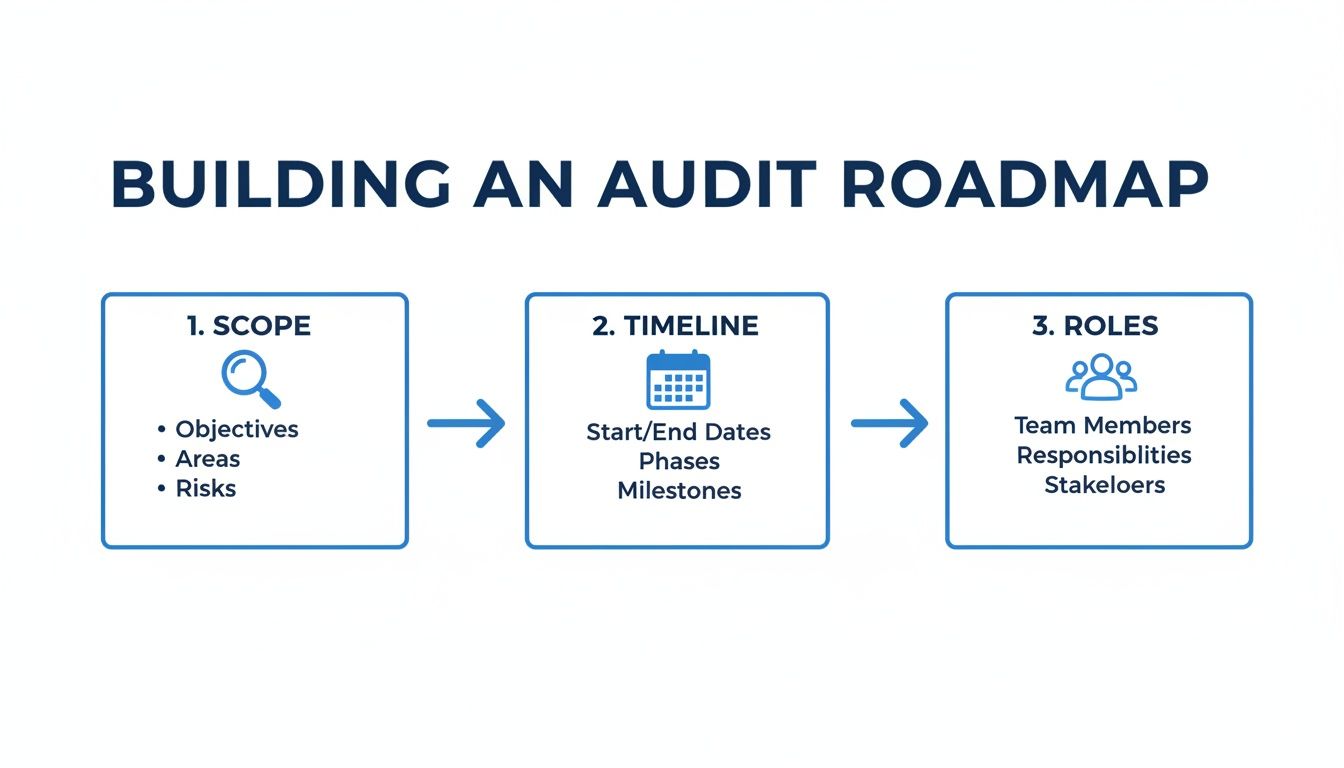
As you can see, moving logically from scope to timeline to roles is the key to building a project plan that actually works.
To get your audit prep started on the right foot, a kickoff checklist can be incredibly helpful. It ensures all initial bases are covered and everyone understands their part from day one.
Audit Preparation Kickoff Checklist
| Phase | Key Action | Primary Owner | Essential Documents |
|---|---|---|---|
| Scoping | Finalize and document the audit's boundaries. | Compliance Lead | Scope Statement, System & Dataflow Diagrams |
| Planning | Develop a detailed project timeline. | Project Manager | Project Plan, Gantt Chart |
| Team | Assign and communicate roles and responsibilities. | Team Leads | RACI Chart, Team Roster & Contact List |
| Kickoff | Hold a kickoff meeting to align all stakeholders. | All | Meeting Agenda, Kickoff Presentation, Action Items |
This table serves as a quick reference to make sure you're not missing any crucial first steps before diving into the heavy lifting of evidence collection.
Set a Realistic Timeline
With your scope locked in, it's time to build a detailed timeline with clear milestones. The best way to do this is to work backward from your audit date. Be honest about how much time you'll need for each phase: collecting evidence, running a gap analysis, fixing what you find, and doing a few dry runs.
I’ve seen it happen a hundred times: teams completely underestimate how long it takes to gather all the necessary evidence, especially in a large organization with siloed departments.
For a more granular breakdown of these initial tasks, our comprehensive audit readiness checklist is a great resource. It lays everything out in a simple, step-by-step format.
One more pro tip: build some buffer time into your schedule. Trust me, something unexpected will come up. A good timeline keeps the pressure from boiling over and helps you avoid that last-minute panic that auditors can smell from a mile away.
Getting Your Evidence in Order: Collection and Organization
Let's be honest, this is where the audit prep gets real. All the planning in the world means nothing without the proof to back it up. Your evidence is the bedrock of a successful audit; without it, your controls are just words on a page.
Your starting point is almost always the auditor's request list, often called the "Provided by Client" or PBC list. Think of this as your audit syllabus—it tells you exactly what documentation you need to pull together. This could be anything from high-level security policies to granular system logs, incident reports, and employee training records. Your job is to gather every single item and organize it in a way that tells a clear, convincing story of your compliance.
The biggest rookie mistake I see is teams just dumping files into a shared drive. It creates instant chaos. You'll waste countless hours hunting for documents and dealing with version control nightmares. The only way to win is to build a centralized, audit-ready repository from day one.
Build a Central Evidence Library
Your goal here is to create a single source of truth for every piece of documentation related to the audit. This isn’t just about storage; it's about creating an intuitive structure. I recommend setting up a logical folder system named after the audit framework's control families, like "Access Control," "Incident Management," and so on. This makes finding specific evidence a breeze for both your team and, crucially, for the auditor.
For instance, if you're gearing up for a SOC 2 audit, you could create top-level folders for each Trust Services Criterion: Security, Availability, Processing Integrity, Confidentiality, and Privacy. Inside each of those, you'd build subfolders for the individual controls, housing the specific policies, screenshots, and logs that prove you're meeting that requirement.
This kind of proactive organization does more than just save you time. It sends a powerful message to the auditor that you're prepared and professional, which can set a positive tone for the entire engagement.
An auditor's confidence in your organization skyrockets when they can easily find what they need. A messy, disorganized evidence repository immediately raises red flags and invites deeper, more time-consuming scrutiny.
Think of it as an open-book test. All the answers are in your documentation, but if you can't find them when the clock is ticking, you're in trouble. A well-organized library is your best friend.
Map Your Evidence to the Requirements
Collecting the evidence is only half the battle. You have to explicitly connect each piece of proof to a specific compliance requirement. This mapping process is non-negotiable. It creates a clear, traceable line from the rule to your proof, leaving no room for ambiguity. If you don't do this, you're essentially handing the auditor a pile of puzzle pieces and asking them to put it together themselves.
You can do this with a straightforward spreadsheet or use a dedicated compliance management tool. The important part is to list every single control and link it directly to the file path of the evidence that satisfies it.
You'll find yourself collecting a few key types of evidence over and over:
- Policies and Procedures: The official documents that outline your company's rules on security, data handling, and key operations.
- System Configurations and Logs: Hard proof, like screenshots and log files, showing your controls are actually implemented (e.g., firewall rules, user access lists, password settings).
- Meeting Minutes: Records from security or risk management committee meetings that demonstrate formal oversight and decision-making.
- Incident Reports: Documentation that walks through how you handled security incidents, from the moment of detection to final resolution.
- Employee Training Records: Proof that your team has been properly trained on the policies and procedures you claim to follow.
If you're looking for a good framework to get started, our guide on creating effective IT audit checklists can really help you structure this part of the process.
Don't Fall into These Common Traps
As you get into the rhythm of collecting evidence, be mindful of a few common pitfalls that can trip up even experienced teams.
A huge one is version control. I can't stress this enough: you must provide the version of a policy or procedure that was active during the audit period. Handing over a policy you just wrote last week as evidence for last year's operations is a critical, and surprisingly common, mistake.
Another classic error is submitting incomplete evidence. A screenshot of a system setting is a start, but a screenshot that also clearly shows a timestamp and the system URL is far more compelling. Always aim to provide full context so the auditor doesn't have to come back with a list of follow-up questions. Make their job easy, and they'll make your life easier.
Running an Effective Gap Analysis
Now that you've collected and mapped your evidence, it's time for the most critical phase of your preparation: the gap analysis. Think of this as your internal pre-audit. It's the dress rehearsal where you get to find—and fix—all the problems before the real auditors walk through the door. This is your single best chance to see where your controls are solid and, more importantly, where they fall short.
This isn't just about checking off boxes. A proper gap analysis means taking a deep, honest look at your current practices versus the standard you're being audited against. The goal is to uncover every weakness, misinterpretation, or piece of missing evidence so you can deal with it now. Skipping this step is like cramming for a final exam the night before. You're just walking in blind and hoping for the best, which is never a good strategy.
All that evidence you just organized? That's the raw material for your gap analysis. This process is where you interrogate those documents to see if they truly meet every single requirement.
The Manual Grind vs. Automated Insight
Traditionally, gap analyses have been grueling, manual affairs. I've seen teams spend weeks, sometimes months, hunched over massive spreadsheets, painstakingly cross-referencing hundreds of pages of policies against dense compliance frameworks. Not only is this approach painfully slow, but it's also incredibly vulnerable to human error. It’s far too easy to miss a subtle requirement or misinterpret a control when you’re swimming in documentation.
For example, a junior analyst might see that a policy for quarterly access reviews exists and check the box. But they could easily miss the specific clause in the framework requiring that review to be conducted by the user's direct manager. That one small oversight can turn into a major finding during the actual audit. Manual methods just don't scale, especially with today's complex regulations.
This is exactly why automated solutions are becoming so essential. Modern tools can ingest all your documentation and instantly compare it against any framework, pinpointing discrepancies with a level of precision that a manual review can't match.
Embracing AI for Faster, Deeper Evidence Discovery
New technology, especially AI-powered platforms, is completely changing the gap analysis game. Imagine uploading your entire evidence library—policies, procedures, system configurations, you name it—and having an AI agent read and reason over every single document. This is what tools like AI Gap Analysis were built to do.
Instead of a person spending 80 hours just reading through documents, an AI can generate a detailed analysis in minutes. And it doesn't just flag a potential gap. It gives you a clear explanation, cites the exact page in your documentation where the evidence is weak or missing, and links directly back to the specific control requirement. This lets you verify everything instantly and start collaborating on a fix.
For a deeper look at the methodology behind this, check out our complete guide on how to conduct a gap analysis.
The table below breaks down the practical differences between the old way and the new way.
Manual vs. AI-Powered Gap Analysis
| Feature | Manual Gap Analysis | AI-Powered Gap Analysis |
|---|---|---|
| Speed | Weeks or months | Hours or days |
| Accuracy | Prone to human error, missed details | High precision, flags subtle gaps |
| Resource Cost | High; requires significant team hours | Low; frees up team for strategic work |
| Evidence Citing | Manual lookup, time-consuming | Automatic, links to exact document page |
| Scalability | Poor; struggles with complex frameworks | Excellent; handles multiple frameworks easily |
| Collaboration | Difficult; based on spreadsheets/emails | Centralized within the platform |
As you can see, the right tool doesn't just make the process faster—it makes it fundamentally better.
The real power of an AI-driven gap analysis isn't just speed—it's accuracy. By augmenting human expertise, these tools can identify subtle gaps that are frequently missed during manual reviews, significantly reducing the risk of unexpected audit findings.
This hybrid approach, where technology does the heavy lifting of discovery and humans provide the critical judgment and context, is the future of audit preparation. It allows you to build a much more resilient compliance program with far greater confidence.
The Growing Need for Augmented Expertise
The pressure on compliance and audit teams has never been higher. According to The IIA's Risk in Focus report, cybersecurity is now the top audit priority, cited by 69% of internal auditors globally and a staggering 87% in North America. At the same time, a concerning 42% of audit teams admit they lack key skills in cybersecurity, AI, and data privacy.
This talent gap means organizations have to find smarter ways to work. Real-world results bear this out: one tech firm preparing for its ISO 27001 audit with an AI-driven tool saw a 40% reduction in audit findings. Why? Because manual evidence hunts often miss up to 30% of relevant evidence. You can find more insights in The IIA's comprehensive 2025 report on global risk priorities.
Ultimately, running an effective gap analysis is about turning unknowns into knowns. Whether you use a spreadsheet or an advanced AI tool, the goal is the same: find every potential issue so you can create a targeted plan to fix it. This single phase, more than any other, determines whether you walk into your audit feeling prepared or just hoping for the best.
Turning Findings Into Fixes with a Remediation Plan
Finding gaps during your analysis is a big step, but it’s what you do next that really counts. Honestly, identifying a weakness is only half the battle. The real work is turning those findings into a documented, actionable remediation plan that builds a stronger, more resilient compliance program. This isn't just about patching holes; it's about systematically turning weaknesses into verifiable strengths.
Think of a well-structured remediation plan as your roadmap for closing every single gap you've found. It’s also a powerful signal to auditors. It shows them you not only recognize your shortcomings but also have a mature, thoughtful process for addressing them. This kind of proactive approach speaks volumes about your commitment to doing things right, and it can genuinely shift the tone of the entire audit.
Prioritize Your Findings Based on Risk
Let's be realistic: not all findings are created equal. The first thing you have to do is prioritize your list of gaps. If you try to fix everything at once, you'll just burn out your team and accomplish very little. The key is to triage these issues based on their real-world impact on the business.
A simple risk matrix is a great tool for this. You can categorize each finding as High, Medium, or Low risk. A High-risk finding might be something glaring, like missing multi-factor authentication on admin accounts. A Low-risk finding could be a minor inconsistency in a policy document.
When you're weighing these, think about a few key factors:
- Severity: If this issue were exploited, how bad would the damage be?
- Likelihood: What are the actual chances of this happening or being found by a bad actor?
- Business Impact: What’s the potential fallout for our operations, reputation, or bottom line?
- Regulatory Fines: Is this a direct violation that could lead to a hefty penalty?
This risk-based approach ensures your team's energy is spent where it matters most. You'll tackle the biggest fires first, knowing you have a plan for the smaller smoldering issues.
Assign Clear Ownership and Deadlines
Once your list is prioritized, every single item needs an owner. This is where a lot of plans fall apart—ambiguity is the enemy of progress. Each task must be assigned to a specific person or team who is responsible for seeing it through to the end. No exceptions.
And with ownership comes a deadline. Vague timelines like "ASAP" are useless. You need to set specific, realistic dates for completion. This creates accountability and makes it possible to actually track progress. So, instead of a task like "Fix server misconfiguration," it should be something like, "Remediate outdated TLS protocol on server XYZ. Owner: Jane Doe. Due Date: March 15th."
A remediation plan without clear owners and firm deadlines is just a wish list. True progress only happens when individuals are empowered and held accountable for driving specific fixes to completion.
This structure is what allows a project manager or compliance lead to keep a clear view of the entire effort, spot bottlenecks before they become major problems, and give leadership an accurate picture of where things stand. Without it, things just fall through the cracks.
Document Everything for the Audit Trail
As you work through your remediation plan, you have to document everything. I can't stress this enough. For every single finding you address, you need to create a crystal-clear audit trail that proves you fixed the problem. This documentation isn't just for you; it's a critical piece of evidence for your auditors.
For each fix, your documentation should include:
- What was fixed: A simple, clear description of the change that was made.
- Who fixed it: The person or team who did the work.
- When it was fixed: The exact date the remediation was completed.
- Proof of the fix: This is the most important part. Include screenshots, updated configuration files, new policy documents—whatever tangible evidence you have that proves the issue is resolved.
This evidence trail is your proof that you took the gap analysis seriously and followed through. It closes the loop on each finding, transforming what could have been an audit failure into a powerful demonstration of your company's commitment to security and compliance. This is how you walk into an audit with real confidence.
Time for a Dress Rehearsal: Dry Runs and Final Evidence Packaging
You've spent weeks, maybe even months, closing gaps and shoring up defenses. Now it's time to see how it all holds up under pressure. This is where a full-on dress rehearsal—what we call a dry run—becomes your most valuable tool. Think of it as a final, comprehensive performance check. It's not just about practicing; it's about systematically rooting out any remaining surprises and building the team's confidence for the main event.
This final stage is all about polish. We'll walk through how to conduct a genuinely useful dry run, get the right people in the room, and use the feedback to make those crucial last-minute tweaks. From there, we’ll move to the last, make-or-break step: packaging all your evidence so professionally that you make the auditor's job—and by extension, your own—a whole lot easier.

Run a Mock Audit That Feels Real
A dry run needs to mimic the real audit as closely as possible. The objective here isn't just to check your documentation but to test your team's ability to present it under pressure. You’re looking to find those awkward handoffs, confusing explanations, or misplaced documents before an external auditor is sitting across the table.
Here's how to structure a mock audit that actually works:
- Designate an "internal auditor." Pick someone who is detail-oriented but wasn't directly involved in the day-to-day evidence gathering. Their mission is to play the part, asking tough questions and demanding to see evidence on the spot.
- Work from the official request list. Don't wing it. Go through the auditor's PBC list item by item, exactly as they will.
- Clock your response times. Pay attention to how long it takes the team to retrieve specific files. If it takes five minutes to find a key policy document, that’s a clear signal your organizational system needs another look.
The insights you gain from this are gold. You might discover a key subject matter expert stumbles when explaining their process, or that a critical report is buried three folders deep under a nonsensical name.
The real win in a dry run isn't a perfect score—it's finding all the reasons you might fail. It’s your chance to fix high-stakes problems in a low-stakes setting before it truly counts.
Get Your Team Ready for Auditor Interactions
The dry run is also your best opportunity for interview prep. Auditors don’t just read; they talk to your people to confirm that the processes on paper are actually being followed. Use your mock audit to role-play these interviews with key stakeholders.
Coach your team on a few simple but powerful communication rules. They should answer questions directly and honestly, but without volunteering extra, unasked-for information. It's also critical to remind them that "I don't know, but I can find out" is a perfectly valid—and often, preferred—answer. This kind of practice goes a long way in reducing anxiety and helps your team present a confident, unified front.
Assemble the Final Evidence Package
Once the dry run is done and you've made your final tweaks, it's time to assemble the final package. Don't underestimate this step; how you present your evidence says a lot. A well-organized, easy-to-navigate package signals professionalism and immediately sets a positive tone for the audit.
Your submission should be much more than just a data dump. Start by creating a master evidence list or index, usually in a spreadsheet. This document should map every single control requirement to the specific evidence file that satisfies it, complete with a direct link to that file in your central repository. For the auditor, this index becomes their roadmap, making their review process incredibly efficient.
Inside that repository, use a clean and logical folder structure that mirrors the audit framework's control families. File names need to be descriptive and consistent (e.g., Policy_Access_Control_v1.2_2024.pdf instead of access policy). These small details save everyone from the headache of hunting for poorly labeled documents.
This level of meticulous preparation is fast becoming the standard. The IIA's new Global Internal Audit Standards, which become mandatory in early 2025, are already pushing for more strategic, tech-enabled audit approaches. This shift comes as 73% of GRC leaders anticipate that their top risks will intensify over the next three years. For example, one medical device operations leader, facing a daunting ISO 13485 audit, used AI to instantly verify findings. The result? They passed with only minor notes, a stark contrast to major non-conformances in previous years. You can learn more about these trends from Deloitte's insights on internal audit hot topics for 2025.
Finally, pull everyone together for one last pre-audit briefing. Go over the schedule, confirm who is speaking to which controls, and do one final review of the communication ground rules. This sync-up ensures everyone is aligned and ready to turn a potentially stressful audit into a smooth, professional engagement.
Tackling Your Toughest Audit Prep Questions
Even with the best-laid plans, preparing for an audit always throws a few curveballs. Knowing how to handle these common hiccups is what separates a stressful audit from a smooth one. Let's walk through some of the most frequent questions I hear from teams on the ground, with practical advice to keep you moving forward.
"The auditor is asking for something that wasn't on our list. What now?"
First, don't panic. This happens all the time and it’s almost never a sign that something is wrong. Auditors are trained to follow a trail. They might see a piece of evidence that naturally leads to a follow-up question, prompting them to ask for a related document that wasn’t on the initial Provided by Client (PBC) list.
The best thing you can do is stay calm and professional. Resist the urge to push back or immediately say you don't have it. Simply acknowledge the request and ask for a moment to track it down with your team. This brief pause gives you the space to find the right document and confirm it’s what they’re actually looking for.
When you respond promptly and with organized evidence to these surprise requests, it sends a powerful message: you're prepared, you're transparent, and you know your stuff. That goes a long way in building trust with your auditor.
"Seriously, how long is this going to take?"
This is the million-dollar question, isn't it? While every company is different, the single biggest mistake I see is underestimating the prep time. The audit itself—the part where the auditor is actively engaged with you—might only last a week or two. But the real work, the heavy lifting, happens in the months leading up to it.
For a first-time certification like ISO 27001 or SOC 2, a good rule of thumb is to budget three to six months for preparation. That timeline covers everything from initial scoping and collecting evidence to running a gap analysis, fixing what you find, and doing a dry run.
Here’s a rough breakdown of how that time gets spent:
| Phase | Estimated Duration | What You're Doing |
|---|---|---|
| Initial Planning & Kickoff | 2-4 weeks | Defining the scope, getting the right people involved, setting a project plan. |
| The Great Evidence Hunt | 4-8 weeks | Gathering every policy, procedure, system log, and record needed. |
| Gap Analysis | 2-3 weeks | Comparing what you have against what the standard requires to find any holes. |
| Remediation Work | 4-10 weeks | The real meat of the project: fixing issues, updating controls, and documenting it all. |
| Dress Rehearsal & Final Polish | 1-2 weeks | Running a mock audit to test your readiness and packaging the final evidence. |
Of course, this can be faster if you already have a strong compliance program. But if you uncover major gaps, you’ll be glad you gave yourself the extra time to fix them properly.
An audit is a marathon, not a sprint. Rushing the preparation phase is a surefire way to have small details slip through the cracks—and those are the exact things auditors are paid to find.
"How do we keep everyone on the same page without endless meetings?"
Getting multiple teams to work together is easily one of the biggest hurdles. The secret is to have one central hub for everything and a predictable rhythm for communication.
First, create a single source of truth. It could be a project management tool like Asana or Jira, a dedicated channel in Slack, or even just a meticulously organized shared drive. The tool itself is less important than everyone’s commitment to using it for all audit-related tasks and documents.
Next, establish a communication cadence that keeps people informed without flooding their inboxes.
- Weekly Team Syncs: Quick, 30-minute stand-ups for the core audit team. Focus only on progress, roadblocks, and what’s next.
- Bi-Weekly Stakeholder Updates: A simple email summary for leadership and department heads. Keep it high-level: here’s where we are, here’s what’s coming, and here’s where we might need your help.
- Crystal-Clear Ownership: Use a simple RACI (Responsible, Accountable, Consulted, Informed) chart. It completely eliminates confusion over who is supposed to deliver what.
This structure prevents the "too many cooks" problem and ensures that when an auditor asks a question, you know exactly who to turn to for the answer.
"What’s the best way to actually answer an auditor’s question?"
How your team communicates with the auditor is just as important as the evidence you hand over. I always coach subject matter experts on a few simple rules to make sure these conversations are productive, not painful.
First, listen to the entire question. It’s human nature to start formulating an answer before the other person has even finished speaking. Don’t. Let them get the full question out before you respond.
Second, be direct and answer only what was asked. It's tempting to offer extra context or share related information to show how much you know, but that can inadvertently open up new lines of questioning and expand the scope of the audit.
And finally, remember that "I don't know, but I will find out" is a perfectly valid—and often, the best—answer. It’s a thousand times better than guessing or giving wrong information. It shows you’re honest and committed to accuracy, which is exactly what an auditor wants to see.
Ready to accelerate your audit preparation and eliminate the guesswork? With AI Gap Analysis, you can upload your documents and let our AI agent instantly identify gaps, cite evidence, and build an audit-ready report in minutes. Stop the manual grind and start your next audit with confidence. Get started with AI Gap Analysis today.