February 12, 2026
assess vendor riskvendor risk managementthird-party riskISO 27001GRC framework
Assess Vendor Risk: A Practical Guide to (assess vendor risk)
Discover how to assess vendor risk with a modern framework. This guide covers vendor tiering, evidence collection, risk scoring, and ongoing monitoring.
20 min readAI Gap Analysis
Assessing vendor risk is all about systematically identifying, evaluating, and ultimately reducing the threats your third-party suppliers can introduce. This isn't just a bureaucratic exercise. We've all seen how a single vendor failure can lead to catastrophic financial, operational, and reputational damage. It requires moving beyond simple checklists to build a supply chain that's not just compliant, but genuinely resilient.
Why You Need a Modern Approach to Assess Vendor Risk
Let's be honest, old-school vendor risk assessments just don't cut it anymore. Your supply chain is more complex and interconnected than ever, and a single third-party breach can derail your entire operation. Trying to manage that dynamic environment with static, check-the-box methods is a recipe for disaster.
The reality is that third-party incidents are skyrocketing. These aren't minor hiccups; they are major events that cause real financial and reputational harm. When a key supplier suffers a data breach or an operational failure, the shockwaves hit your organization directly, eroding customer trust and your bottom line.
The Failure of Traditional Methods
I’ve seen it time and again: manual processes are slow, wildly inconsistent, and rarely paint an accurate picture of a vendor's security posture. A questionnaire filled out once a year is just a snapshot in time. It's often outdated the moment it’s submitted, leaving you blind to new risks that pop up between those long assessment cycles.
The core problem with legacy assessments is that they are reactive, not proactive. They tell you what a vendor's risk posture was, not what it is right now. That gap is precisely where catastrophic breaches happen.
Embracing a Structured Framework
Adopting a modern, structured framework to assess vendor risk isn't optional anymore—it's an essential business practice. And this goes way beyond just satisfying auditors or ticking a compliance box. This is about building true operational resilience.
A structured approach ensures that:
- Risks are consistently identified: You have a repeatable, reliable process for evaluating every single vendor.
- Prioritization is data-driven: You can focus your limited time and resources on the suppliers that pose the greatest threat to your business.
- Decisions are defensible: You have a clear audit trail showing why a vendor was approved and exactly how their risks are being managed.
The market is catching on to this shift in a big way. The global Vendor Risk Management (VRM) market was valued at USD 11.1 billion in 2024 and is projected to surge to USD 39.69 billion by 2033. You can dig into the drivers of this growth on straitsresearch.com.
This explosive growth reflects the urgent need for organizations to get a handle on third-party vulnerabilities. New technologies are completely changing the game, setting the stage for the practical, automated strategies we'll explore. For more on this, check out our guide on AI for regulatory compliance.
Building Your Vendor Risk Assessment Framework
Let's be honest: a one-size-fits-all checklist for vendor risk is a recipe for disaster. To build a program that’s both scalable and defensible, you need a strategic framework. Think of it as your blueprint for creating a repeatable, proactive process that truly protects your organization, moving you from constantly putting out fires to strategically managing risk.
The first, and arguably most critical, step is classifying your vendors. This is what keeps your team from spending weeks assessing the office coffee supplier with the same rigor as your cloud hosting provider. It’s all about focusing your energy where the risk is highest—on the vendors holding the keys to your kingdom.
Classifying Vendors into Risk Tiers
The core idea here is simple: not all vendors are created equal. A marketing agency running a social media campaign just doesn't carry the same level of risk as a SaaS platform that processes all of your customer PII. To make this work, your classification criteria need to be crystal clear, documented, and applied consistently across the board.
When you're building your tiering logic, here are the factors I always recommend focusing on:
- Access to Sensitive Data: Does the vendor process, store, or transmit personally identifiable information (PII), protected health information (PHI), or your company’s confidential financial data? This is often the biggest red flag.
- Operational Criticality: What happens if this vendor goes down? If they have an outage, does it grind your business to a halt, or is it a minor inconvenience?
- Regulatory Scope: Does the service they provide pull them (and you) into the scope of regulations like GDPR, HIPAA, or PCI DSS?
- Financial Impact: What's the potential financial fallout—direct or indirect—if this vendor suffers a breach or simply fails to deliver on their promises?
To give you a practical starting point, here’s a sample matrix for how you might tier vendors.
Vendor Risk Tiering Matrix Example
This table provides a sample framework for classifying vendors into tiers based on their access to sensitive data and their operational criticality, helping teams prioritize their assessment efforts.
| Tier Level | Data Access Level | Operational Criticality | Assessment Frequency |
|---|---|---|---|
| Tier 1 (Critical) | Direct access to PII, PHI, or sensitive intellectual property. | Essential for core business operations; a failure would cause significant disruption. | Annually (or upon major changes) |
| Tier 2 (High) | Access to confidential business data (non-PII) or integrated into key business processes. | Important for business functions; a failure would cause moderate disruption. | Every 18-24 months |
| Tier 3 (Moderate) | Limited access to non-sensitive data; provides non-critical services. | Supports non-essential functions; a failure would have minimal impact. | Every 36 months |
| Tier 4 (Low) | No access to company data or systems. | Non-business-related services (e.g., office supplies). | Initial screening only |
This kind of structure immediately clarifies where your team should spend its time and resources.
The shift away from outdated, static reviews toward a more dynamic, ongoing approach is critical in today's environment. It's no longer enough to check a box once a year.
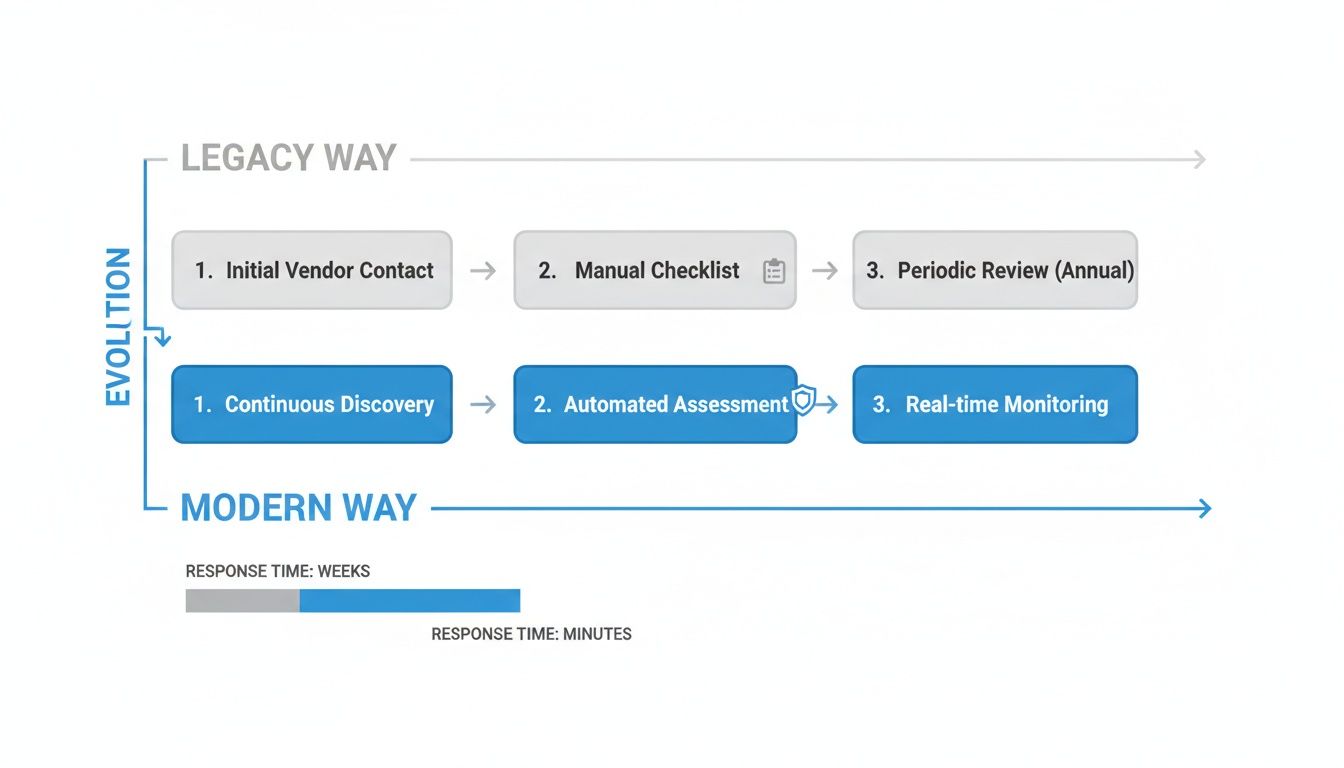
This change is fundamental. We're moving from a snapshot in time to a continuous film, which is the only way to keep up with evolving threats.
A well-defined tiering structure is the foundation of an efficient vendor risk program. It ensures that your level of due diligence is directly proportional to the level of risk a vendor introduces.
Establishing a Governance Structure
Once you have your tiering logic sorted out, the next piece of the puzzle is governance. This isn't about creating endless red tape. It’s about defining clear ownership and accountability so that when a high-risk issue pops up, everyone knows their role. No more finger-pointing.
A solid governance model clearly defines three things:
- Roles and Responsibilities: Who is the business owner for the vendor relationship? Who is ultimately responsible for conducting the risk assessment? And critically, who has the final authority to approve or reject a vendor?
- Assessment Workflows: What are the actual steps for assessing a Tier 1 vendor versus a Tier 3? This should spell out the exact questionnaires to use, the evidence you'll require, and how often you'll perform a review.
- Escalation Paths: What happens when an assessment uncovers a risk that’s too hot to handle—something that exceeds your organization's risk appetite? You need a formal, documented process for escalating that issue to senior leadership for a final decision.
Defining these elements upfront transforms vendor risk management from a chaotic, ad-hoc scramble into a predictable and manageable business function. It’s this structure that makes your program truly defensible to auditors and regulators, proving you have a thoughtful, risk-based approach. The entire framework should be documented and easy to find, acting as the single source of truth for how your organization manages third-party risk.
Gathering Meaningful Evidence and Mapping Controls
Now that you have your vendors tiered and a solid framework in place, it’s time to roll up your sleeves. This is where the real work begins—gathering the right evidence, asking the tough questions, and mapping everything back to the standards that matter to your business.
It’s about more than just collecting documents. Anyone can ask for a stack of PDFs. The goal is to extract genuine insights that tell you how a vendor actually operates. A three-year-old SOC 2 report or a boilerplate security policy doesn't tell you much about their current security posture. You need timely, relevant evidence that proves their controls are not just designed well, but are actively working.
Moving Beyond Simple Checklists
Standard security questionnaires are a good starting point, but let’s be honest, they’re notoriously unreliable on their own. We've all seen vendors check "yes" to every box. But simple yes/no answers just don't cut it anymore, especially when third-party breaches are a massive concern.
Consider this: 97% of organizations were hit by at least one supply chain attack in the last year. That risk gets amplified when you realize the average company shares sensitive data with nearly 300 different vendors. To make matters worse, legacy assessment methods are failing us—a startling 4% of compliance professionals actually trust their questionnaires to reflect a vendor's true risk. You can dig into more of these third-party risk stats over at atlassystems.com.
To get real answers, you have to ask for proof. The shift is subtle but powerful.
Instead of asking, "Do you have an incident response plan?"
Try this: "Please provide your current incident response plan, along with the date of its last test, a summary of the results, and any remediation actions you took."
This simple change moves the conversation from if they have a control to demanding evidence of that control in action. It’s the quickest way to separate the vendors just talking a good game from those who are truly on top of their security.
Key Evidence to Request
The documents you ask for should be directly tied to the vendor's risk tier. A Tier 1 vendor swimming in your sensitive PII needs a much deeper look than a Tier 3 marketing tool.
Here’s a practical breakdown of what to ask for, based on risk level:
-
For High-Risk Vendors (Tier 1 & 2):
- Third-Party Attestations: This is non-negotiable. Think SOC 2 Type II reports, ISO 27001 certificates, or HITRUST CSF certifications. An independent auditor has already done a lot of the heavy lifting for you.
- Penetration Test Results: Always ask for the executive summary from a recent (within the last 12 months) third-party pen test.
- Key Policy Documents: You'll want to see their Information Security Policy, Incident Response Plan, and their Business Continuity/Disaster Recovery (BC/DR) plans.
- Data Flow Diagrams: If they're processing your data, you need to know exactly how it moves through their systems.
-
For Moderate-Risk Vendors (Tier 3):
- Standardized Questionnaires: A well-constructed questionnaire like a CAIQ or SIG Lite is often perfectly sufficient here.
- Proof of Key Certifications: If they claim to be ISO certified, ask for the actual certificate.
- Insurance Certificates: Make sure they have adequate cyber liability insurance. It’s a good backstop.
Mapping Evidence to Controls with Automation
Once the evidence starts rolling in, the next big hurdle is connecting it all back to the specific controls in your required frameworks, whether that’s ISO 27001, ISO 13485, or another standard.
Manually digging through a 100-page SOC 2 report to find evidence for a single control is a soul-crushing, error-prone task. It’s slow, tedious, and frankly, a poor use of your team’s expertise.
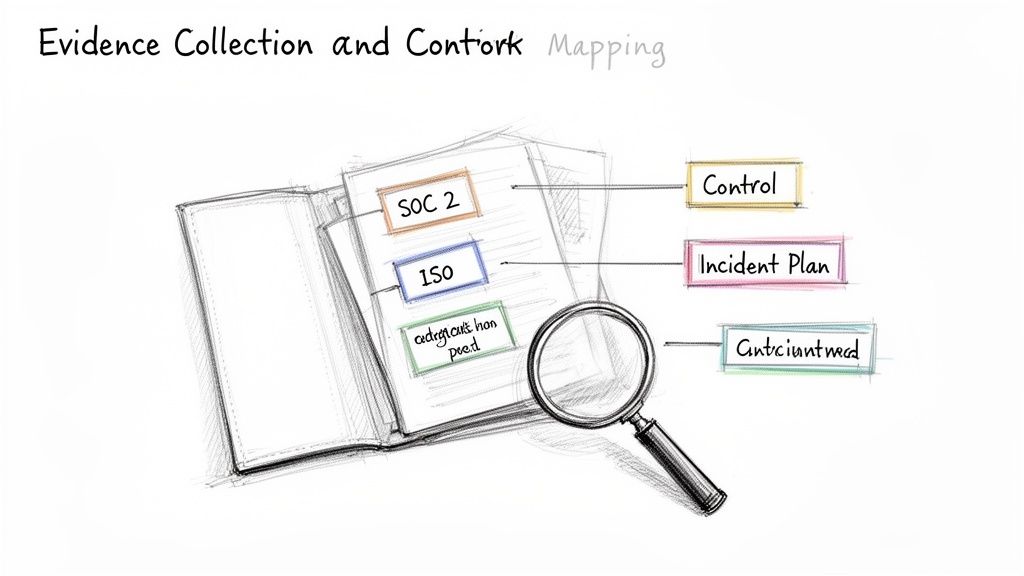
This is where modern tools completely change the game. Instead of spending days playing "find the keyword," you can use AI to do the heavy lifting. We explore this in more detail in our article on the modern gap assessment process.
With an AI-powered platform, you can instantly extract relevant sentences, paragraphs, and data points from a vendor’s documentation and see it mapped directly to a specific control requirement, complete with citations.
This kind of automation turns the most painful part of vendor assessment into a far more manageable workflow. Your team can immediately see where the evidence is strong, where it’s weak, and exactly where the compliance gaps are. This frees you up to focus on what really matters: analyzing the findings and mitigating the risk.
From Findings to Actionable Risk Scores
So, you’ve collected the evidence and mapped it to your controls. This is the point where a lot of teams hit a wall, buried under a mountain of PDFs and questionnaire answers. The next, and most critical, move is to translate all that raw data into clear, quantifiable risk scores. These scores need to be simple enough for everyone—from your CISO to the business unit owner—to grasp instantly.
This isn’t about inventing some complex, black-box algorithm. It’s about applying consistent, defensible logic to separate the signal from the noise. For instance, an unpatched server at a Tier 3 marketing vendor is a concern, sure. But it’s a world away from a critical SaaS provider that doesn't have a formal incident response plan. A scoring system gives you the language to explain that difference clearly.
Boiling a finding down to a score forces you to think about two fundamental dimensions of risk: likelihood and impact. Likelihood is just what it sounds like—the chance of a threat actually exploiting a vulnerability. Impact is the damage it would cause if it did, whether that’s financial, reputational, or operational.

Building a Practical Risk Scoring Rubric
To score anything consistently, you need a rubric. Think of it as your team’s single source of truth for evaluating vendor risk. It ensures that two different analysts looking at the same issue will land on a similar conclusion, removing guesswork from the equation. A simple 5x5 matrix is usually the most effective tool for this job.
A good scoring rubric standardizes your assessments, prevents purely subjective judgments, and creates a clear, auditable trail for every decision you make.
Here's a straightforward example of a rubric you can adapt. It helps you quickly turn an observation into a priority level with a clear next step.
Sample Risk Scoring Rubric
| Risk Level | Impact (1-5) | Likelihood (1-5) | Score Range | Required Action |
|---|---|---|---|---|
| Critical | High (4-5) | High (4-5) | 16-25 | Immediate remediation required; business owner escalation. |
| High | High (4-5) | Low (1-3) | 10-15 | Remediation plan due within 30 days. |
| Moderate | Low (1-3) | High (4-5) | 10-15 | Remediation plan due within 60 days. |
| Low | Low (1-3) | Low (1-3) | 1-9 | Risk accepted or remediated at vendor's discretion. |
With a model like this, a finding stops being just a vague "red flag." It becomes a number that triggers a specific, predefined action.
The Central Role of the Risk Register
Every single scored finding needs a home. This is where a risk register comes in. It’s a central log—it can be a sophisticated feature in a GRC platform like Hyperproof or even a well-organized spreadsheet—that tracks every identified risk from the moment it’s discovered until it’s closed. This document is your command center for remediation.
For every entry, make sure you capture these key details:
- Risk Description: A quick, clear summary of the issue.
- Vendor & Service: Which partner and what service is affected.
- Impact & Likelihood Scores: The numbers from your rubric.
- Overall Risk Score: The final calculated score (Impact x Likelihood).
- Remediation Owner: The single person accountable for getting it fixed.
- Status: Is it Open, In Progress, Remediated, or has the risk been formally Accepted?
This register quickly becomes one of your most valuable tools, not just for tracking progress but also for reporting up to leadership and proving due diligence to auditors.
A well-maintained risk register transforms your vendor risk program from a series of isolated assessments into a living, breathing management system. It's the bridge between identifying a problem and actually solving it.
Communicating Findings and Driving Remediation
Nobody likes being handed a long list of critical problems. If you just drop a report on a business owner’s desk, expect panic and defensiveness. The trick is to frame the conversation around partnership and enabling the business, not pointing fingers. Lead with your highest-priority findings and come to the table with realistic, actionable recommendations.
This collaborative approach almost always gets better and faster results. The old manual assessment methods are already breaking at scale. Consider that 40% of organizations send an average of 55 questionnaires a year. Despite all that work, 60% of cybersecurity leaders see third-party threats as "innumerable and unmanageable," and nearly half of all companies experienced a breach originating from a third party in the last year. By working with your vendors, you can cut through the noise. You can find more of these eye-opening third-party risk statistics from Recorded Future.
Embedding Accountability in Your Contracts
Finally, remember that collaboration is great, but it works best when backed by clear contractual obligations. Your master service agreements (MSAs) and statements of work (SOWs) are your most powerful tools for enforcing security accountability.
For any high-risk vendor, there are two clauses that are absolutely non-negotiable:
- Security Requirements: Be explicit. Reference specific standards (e.g., "Vendor must maintain ISO 27001 certification") or spell out mandatory controls.
- Right to Audit: This clause gives you the contractual right to periodically check on the vendor's security controls, whether you do it yourself or hire a third party.
Getting these terms into your contracts sets clear expectations from day one and gives you legal recourse if a vendor doesn't hold up their end of the bargain. It formalizes the entire process to assess vendor risk, turning security into a genuinely shared responsibility.
Maintaining an Always Audit-Ready Posture
Let’s be honest: the job of assessing vendor risk is never really finished. Your initial assessment is just a snapshot in time. The very next day, a vendor’s security posture could shift because of a new subcontractor, a system update, or an emerging threat.
This is why mature vendor risk management programs are moving away from the old-school, periodic check-in. The new goal is to be "always audit-ready." This isn't about scrambling for a few frantic weeks before an audit. It’s about building a program that operates so smoothly that an audit becomes a non-event—just a routine check-up of the great work you're already doing.
Moving from Periodic Reviews to Continuous Insight
The traditional annual questionnaire is broken. In the fast-paced world we operate in, a year is an eternity. A recent study found that a staggering 61% of U.S. companies have dealt with a data breach caused by one of their vendors. Relying on year-old information is like driving while looking in the rearview mirror.
Continuous monitoring is the answer. It’s about creating a system that feeds you timely, relevant intelligence about your vendors’ risk posture. You’re not just filing away a static report; you’re building a living, breathing profile for each partner.
So, how do you make this happen?
- Automated Threat Intelligence: Subscribe to services that watch for public data breaches, security incidents, or even negative press involving your critical vendors.
- Security Ratings Services: Use platforms that constantly scan a vendor's external-facing systems for vulnerabilities. These give you an objective score of their security hygiene, independent of what they tell you.
- Regular Check-ins: For your most critical vendors, this might mean a quarterly call to discuss any significant changes to their environment, key personnel, or security controls.
This shift takes vendor risk from a reactive, check-the-box chore to a proactive, security-first discipline.
The Power of a Centralized Evidence Repository
Being audit-ready means you can prove your due diligence at a moment's notice. When an auditor asks, "How do you know this critical SaaS vendor is securely managing our data?" you can’t afford to spend three days digging through emails and shared drives for an answer.
This is where a centralized platform becomes your best friend. It acts as the single source of truth, connecting every risk to its assessment, the evidence you collected, and the remediation plan you put in place.
An always audit-ready posture isn't about having zero risks. It's about proving you have a robust, repeatable process for finding, evaluating, and managing those risks. The documentation of your process is just as important as the actions you take.
Picture the auditor’s request again. Instead of a frantic scramble, you calmly pull up the vendor’s profile, show the initial assessment, point to real-time monitoring alerts, and display the complete history of every risk and its resolution. That level of organization is what separates a world-class program from an average one. For more hands-on advice, you can explore a comprehensive audit readiness checklist.
Tracking Remediation in Real Time
Finding a risk is only half the job. The other, arguably more important half, is making sure it gets fixed. A truly audit-ready program needs a dynamic link between what you find and what your vendors do about it.
When you identify a gap—say, a vendor doesn’t have a formal data recovery plan—that finding should immediately go into a risk register with a clear owner and a deadline. By using a collaborative platform, both your internal team and the vendor can provide updates directly on that specific issue.
This creates a live, auditable trail. It shows you’re not just flagging problems but actively partnering with your vendors to solve them. This approach accomplishes two critical things:
- Enforces Accountability: It leaves no doubt about who is responsible for the fix and when it’s due, so issues don’t fall through the cracks.
- Provides a Clear Narrative: For an auditor, this tells a complete story from discovery to resolution, proving your program is effective and not just for show.
Ultimately, maintaining an audit-ready posture closes the loop. It transforms your assessment process from a one-off project into a continuous cycle of evaluation, monitoring, and improvement—the foundation of true supply chain resilience.
Common Questions About Vendor Risk Assessment
Even with a solid framework, questions always pop up when you're in the trenches building out a vendor risk program. It's completely normal to wonder if you're focusing on the right things or if there's a more efficient way to get the job done.
Getting clear, practical answers to these common hurdles can help you navigate roadblocks and sharpen your approach. Let's tackle some of the most frequent questions I hear from compliance and regulatory teams.
How Often Should We Re-Assess Our Vendors?
The honest answer? It depends entirely on their risk tier. Applying a one-size-fits-all schedule is a guaranteed way to waste time and resources. Your assessment frequency should be a direct reflection of the risk a vendor introduces to your business.
A practical approach looks something like this:
- High-Risk Vendors (Tier 1): These are your critical partners—the ones handling sensitive data or essential infrastructure. They need a full, deep-dive assessment at least annually. This should be supplemented with continuous monitoring to catch any issues between those formal reviews.
- Moderate-Risk Vendors (Tier 2): For this group, a full reassessment every 18-24 months is a reasonable cadence. This strikes a good balance between thorough due diligence and operational efficiency.
- Low-Risk Vendors (Tier 3 & 4): You can typically review these vendors every two to three years, or whenever their services or your relationship with them changes in a meaningful way.
The key isn't just having a schedule; it's documenting your policy and being able to justify your decisions based on risk. An auditor will care far more about your well-reasoned methodology than the specific timeline itself.
What Are the Biggest Red Flags in a Vendor Assessment?
After you've done this for a while, you start to see patterns. Certain responses or behaviors from vendors are immediate red flags that signal a deeper lack of security maturity. Ignoring them is a gamble you just can't afford to take.
Here are some of the most critical warning signs to watch for:
- Lack of Formal Policies: If a vendor can't produce a basic information security policy or an incident response plan, that's a massive problem. It suggests their security practices are ad-hoc and undocumented.
- No Designated Security Lead: When nobody is clearly responsible for security, it’s almost certain that nobody is owning it. Every organization needs a point person who is accountable for protecting data.
- Pushback on Contractual Clauses: Be wary of any vendor that resists reasonable security clauses, like "Right to Audit" or specific breach notification timelines. They're often hiding something.
- Vague or Evasive Answers: If their questionnaire responses are full of jargon but lack specific details or evidence, you need to dig deeper. A mature vendor will provide clear, confident answers backed by proof.
And, of course, a history of recent, poorly handled breaches is another obvious sign that their incident response capabilities are not up to par.
How Can a Small Team Manage Dozens of Vendor Assessments?
This is the reality for most of us—a small team with a massive workload. The only way to survive, let alone thrive, is to work smarter, not harder. Efficiency has to be at the core of your entire process.
First off, a robust risk-tiering system is non-negotiable. It’s your most powerful tool for prioritization, ensuring your limited time is spent on the vendors that pose the greatest threat. Don't waste a week on a low-risk supplier when a critical one is overdue.
Second, you have to embrace automation. Trying to manually assess dozens of vendors is a losing battle. Modern GRC platforms and AI-powered tools can handle the most time-consuming parts of the job, like parsing through evidence and mapping controls. This allows a small team to achieve what would be impossible otherwise.
Finally, standardize everything you can. Create templates for your questionnaires, communications, and reports. A consistent, repeatable workflow for each risk tier saves mental energy and ensures nothing falls through the cracks.
Ready to stop wasting hours digging through documents and start getting instant, evidence-backed answers? AI Gap Analysis uses AI to read your compliance documents, map findings directly to controls, and highlight gaps in minutes. It's the fastest way to accelerate your vendor assessments and become always audit-ready. See how AI Gap Analysis works.