February 4, 2026
cloud security assessmentscloud security auditcybersecurity frameworkscloud complianceNIST CSF
Cloud security assessments: A concise guide to cloud security assessments
Discover cloud security assessments: learn key types, frameworks, and a practical step-by-step method to secure your cloud infrastructure.
21 min readAI Gap Analysis
Think of a cloud security assessment as a deep-dive health check for your infrastructure living in the cloud. It’s a methodical process designed to hunt down and fix security weaknesses—from sneaky vulnerabilities and misconfigurations to compliance gaps—before an attacker finds them first. This isn't just a good idea; it's an essential practice for anyone serious about protecting data in environments like AWS, Azure, and GCP.
Why Cloud Security Assessments Are Non-Negotiable

Don't mistake a cloud security assessment for just another item on a to-do list. It’s more like an architectural stress test for a new skyscraper. Before anyone sets foot inside, engineers run simulations for everything from earthquakes to gale-force winds to make sure the building is solid. An assessment does the exact same thing for your cloud setup, pushing past theory to prove your defenses can actually handle real-world threats.
This kind of validation is absolutely critical because cloud environments are constantly in motion. A single misconfigured setting on a storage bucket or one user account with too many permissions can open the door for a massive data breach. And when your development teams are pushing changes all the time, these tiny errors can pile up into a major risk without anyone even realizing it.
The Sobering Reality of Cloud Breaches
The sheer number of security incidents has forced businesses to make proactive defense a top priority. It's not hard to see why. Recent data reveals that a staggering 98% of organizations have had at least one cloud data breach, a huge jump from 79% just a few years back. The culprits are often the usual suspects: runtime security gaps, unauthorized access, and basic misconfigurations. This just underscores how badly we need systematic reviews. You can dig deeper into the latest cloud security statistics to understand the trends.
A proper assessment gives you the clarity needed to get in front of these problems. It helps you finally answer the tough questions about your security posture:
- Where is our most sensitive data actually stored in the cloud?
- Who can access it, and do they really need to?
- Are our configurations truly aligned with security best practices and our compliance mandates?
- If we were attacked tomorrow, how would our defenses actually perform?
By methodically evaluating your cloud infrastructure, you shift from a reactive "break-fix" cycle to a proactive state of security readiness. It’s about building a resilient foundation that protects your assets, maintains customer trust, and supports business innovation securely.
At the end of the day, cloud security assessments are your number one tool for proving your security controls are not just in place, but are genuinely working. They give you the hard evidence you need to operate confidently in the cloud, transforming uncertainty into a clear, actionable plan for getting better.
The Core Types of Cloud Security Assessments
When it's time to check your cloud environment's security, it's important to realize that cloud security assessments aren't a one-size-fits-all deal. Each type has a specific job, giving you a different view of your security posture. Think of it like a complete physical for your health—you wouldn’t rely on just a blood test. You’d also get an X-ray and maybe a stress test to see the whole picture.
It's the same with cloud security. A strong strategy mixes several assessment types to cover all your bases. Knowing the core methods helps you pick the right tool for the job, whether you're trying to lock down your infrastructure, test your defenses against a real attack, or prove you meet compliance standards.
H3: Configuration Reviews: Checking the Blueprint
A configuration review is your starting point—the absolute foundation of any cloud assessment. It's like asking a master architect to go over your building's blueprints before construction even starts. This process methodically checks all your cloud settings against proven security standards, like the benchmarks from the Center for Internet Security (CIS).
The whole idea is to find and fix misconfigurations before an attacker can find them. These slip-ups are often the easy wins for criminals. A configuration review gets straight to the point, asking things like:
- Are any of our storage buckets mistakenly open to the public?
- Do our security groups have rules that allow anyone to connect?
- Are we giving out far too many permissions with our Identity and Access Management (IAM) roles?
This is a proactive, preventative measure. It’s all about building security in from the very beginning.
H3: Penetration Testing: Simulating a Real-World Attack
If a configuration review checks the blueprints, a penetration test (or pen test) is like a simulated earthquake hitting your finished building. It’s an active, hands-on test where ethical hackers try to break through your defenses, using the same tactics a real attacker would. This isn't about what might happen; it’s about proving what can happen.
A pen test provides invaluable evidence of exploitability. It moves beyond theoretical risks by demonstrating how a chain of seemingly minor vulnerabilities could lead to a significant data breach, validating the effectiveness of your security controls under pressure.
These testers use their skills to find and exploit weaknesses in your apps, networks, and setups. Their report gives you a brutally honest look at how well you'd hold up in a real attack, helping you fix the most critical issues first.
H3: Compliance Mapping: Aligning with Rules and Regulations
A compliance mapping assessment is all about lining up your security controls with specific industry standards or government regulations. This is a must-do for any organization that has to follow rules like GDPR, HIPAA, PCI DSS, or ISO 27001.
In this assessment, you map what you're currently doing directly to the requirements of a framework. It shines a light on where you're falling short, so you can close those gaps, pass your audits, and avoid massive fines. This is also a huge part of managing third-party risk. To learn more, check out our guide on how to conduct a vendor risk assessment.
H3: The Shared Responsibility Model: Knowing What’s Yours to Secure
The shared responsibility model is a critical concept that shapes every single one of these assessments. Your security duties change drastically depending on whether you're using Infrastructure as a Service (IaaS), Platform as a Service (PaaS), or Software as a Service (SaaS). Getting this right is fundamental to scoping your assessments correctly.
Essentially, the more control you have over the environment (like in IaaS), the more you're responsible for securing. As you move toward SaaS, the cloud provider takes on more of that burden.
The table below breaks down where your security focus needs to be for each model.
Cloud Service Model Assessment Focus (IaaS vs. PaaS vs. SaaS)
| Assessment Area | IaaS (e.g., AWS EC2, Azure VMs) | PaaS (e.g., Heroku, AWS Lambda) | SaaS (e.g., Salesforce, Google Workspace) |
|---|---|---|---|
| Network Controls | Your Responsibility. Configure security groups, subnets, and firewalls. | Shared. You manage application-level network rules; provider manages underlying network. | Provider's Responsibility. The provider manages all networking infrastructure. |
| Identity & Access | Your Responsibility. Manage all user accounts, roles, and permissions. | Your Responsibility. Manage application user access and roles. | Your Responsibility. Manage user accounts, permissions, and data sharing rules. |
| Data Encryption | Your Responsibility. Encrypt data at rest and in transit. | Your Responsibility. Encrypt application data. | Shared. You configure encryption options; provider manages implementation. |
| Operating System | Your Responsibility. Patch and harden the guest OS. | Provider's Responsibility. The provider manages the underlying OS. | Provider's Responsibility. Not applicable to the customer. |
| Application Code | Your Responsibility. Secure your own applications. | Your Responsibility. Secure your own application code. | Provider's Responsibility. The provider secures the application. |
As you can see, even with a SaaS application where the provider handles most of the heavy lifting, you're still on the hook for managing user access and data configurations properly. Understanding this division of labor is the key to a successful—and relevant—cloud security assessment.
Choosing the Right Cloud Security Framework
Trying to run a cloud security assessment without a framework is like trying to build a house without blueprints. It's chaotic, inconsistent, and you'll miss critical things. Frameworks give you that essential structure, a clear and standardized set of best practices that turns a messy process into something systematic and defensible.
Picking the right framework—or, more often, the right combination of them—is one of the most important decisions you'll make. It all comes down to your industry, what regulations you have to follow, and what you’re trying to achieve. Some frameworks are broad, designed for high-level strategy, while others are incredibly specific, giving your engineers a literal checklist to follow.
Think of these frameworks as toolkits. Each one has a different purpose, and knowing which tool to grab for which job is the key to building a truly solid security posture.
The NIST Cybersecurity Framework for Strategic Risk Management
The NIST Cybersecurity Framework (CSF) is your 30,000-foot view. It's the strategic blueprint for your entire security program. Developed by the National Institute of Standards and Technology, the CSF doesn't get into the weeds of how to configure a specific cloud service. Instead, it gives you a common language and a risk-based approach to manage security across your whole organization.
The CSF is built on five core functions that create a continuous loop:
- Identify: Know what you have—your assets, data, and business environment—and the risks associated with them.
- Protect: Put safeguards in place to protect your critical services and data.
- Detect: Have the tools and processes to spot a security event when it happens.
- Respond: Know exactly what to do to contain the impact of an incident once it’s detected.
- Recover: Have a plan to get back on your feet and restore services after an incident.
When you're doing a cloud assessment, the NIST CSF is what helps you connect the technical details back to the business. It’s how you make sure you’re not just chasing down random misconfigurations, but building a program that actually manages risk in a way the rest of the business understands.
CIS Benchmarks for Tactical Configuration Hardening
If NIST is the strategic plan, the Center for Internet Security (CIS) Benchmarks are the tactical, on-the-ground instructions for your engineers. These benchmarks are recognized worldwide as the gold standard for securely locking down IT systems and cloud services.
CIS publishes incredibly detailed hardening guides for just about every major cloud service you can think of, from AWS and Azure to Google Cloud. They give you granular, step-by-step recommendations that your team can follow to the letter.
For an AWS S3 bucket, a CIS Benchmark will tell you precisely how to block public access, mandate server-side encryption, and set up proper logging. It takes all the guesswork out of secure configuration and ensures everyone is doing it the same way.
Using CIS Benchmarks during an assessment gives you a clear, objective measuring stick for your technical setup. You can directly compare how your environment is configured against these best practices, making it easy to spot and fix gaps with surgical precision.
The ISO/IEC 27000 Series for Certified Security Management
The ISO/IEC 27000 family of standards is what you turn to when you need to prove your security maturity to the outside world. Centered around ISO/IEC 27001, this framework is all about building a formal Information Security Management System (ISMS). This is the path you take when big customers or regulators demand an internationally recognized certification.
While ISO 27001 sets the stage for the ISMS, two other standards are particularly vital for the cloud:
- ISO/IEC 27017: This standard provides specific security controls and guidance tailored for cloud environments.
- ISO/IEC 27018: This one focuses on protecting Personally Identifiable Information (PII) in the public cloud, a must-have for anyone handling customer data.
Going down the ISO path is a serious commitment, but it’s a powerful way to show that you have a mature, process-driven security program. For companies in regulated industries or those handling sensitive data, an ISO certification is often the price of entry.
By weaving together the strategic vision of NIST, the technical precision of CIS, and the formal structure of ISO, you create a powerful, layered defense for your cloud environment.
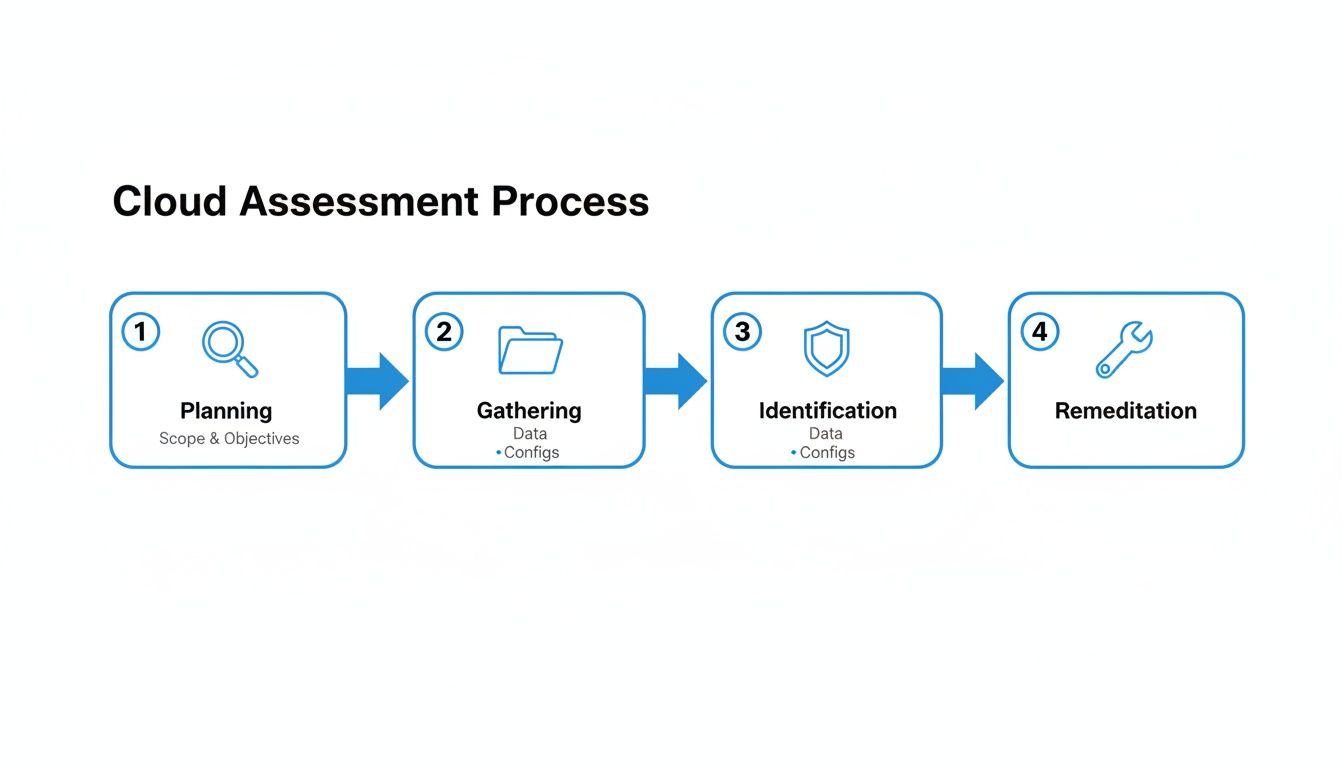
Your Step-by-Step Assessment Methodology
A solid cloud security assessment isn't just a random check of settings; it's a structured, repeatable process. If you treat it like a well-defined project with clear phases, you can turn what feels like a massive, overwhelming task into something completely manageable. By breaking it down, you ensure nothing gets missed, the results are consistent, and you end up with real, actionable steps to actually improve your security.
Think of it as a four-phase mission. It's a logical flow that takes you from planning the operation to celebrating the win. You start by drawing the map, then you gather your intel, identify the weak spots, and finally, you act on that intel and report back on the outcome.
Phase 1: Scoping and Planning
Before you even think about touching a configuration file, you have to define the rules of engagement. Honestly, this first phase is the most critical one. Get this right, and everything else falls into place. Rush it, and you're signing up for scope creep, wasted time, and a final report that doesn’t really tell you anything useful.
First up, figure out what you actually have. You need a complete inventory of every cloud account, subscription, region, and critical application. You can't protect what you don't know exists. Once you have that list, you can start classifying data and apps based on how sensitive they are and how much they matter to the business. This helps you focus your energy where it counts.
Here are the key questions you need to nail down in this phase:
- Which specific cloud accounts and services are we looking at? (e.g., Production AWS, Development Azure)
- What compliance frameworks do we need to measure ourselves against? (e.g., CIS Benchmarks, NIST CSF, ISO 27001)
- Who are the key stakeholders and technical contacts we’ll need to talk to?
- What's the end goal here? (e.g., prepping for an audit, a review after an incident, or just a general posture check-up)
Phase 2: Evidence Gathering and Analysis
With a clear scope defined, it's time to get your hands dirty and start collecting data. This phase is all about connecting to your cloud environments—usually with read-only API access—and systematically pulling information about configurations, permissions, and security controls. This is where you gather the raw, objective facts that will drive your analysis.
The goal here is objective evidence, not just opinions. We’re talking about actual policy documents, configuration settings, and activity logs. For example, instead of just asking an engineer if the IAM roles are secure, you download the JSON policies for every high-privilege role and analyze them line by line.
Effective evidence gathering is the bedrock of a credible assessment. It moves the conversation from "we think we're secure" to "we can prove our controls are configured correctly." This is how you get the verifiable data needed to drive real change.
During this stage, your team will be digging into a wide range of components:
- Identity and Access Management (IAM): Reviewing user roles, permissions, and cross-account trust policies to hunt for any excessive privileges.
- Network Security: Analyzing security group rules, network ACLs, and VPC setups to spot any unnecessary exposure to the internet.
- Data Protection: Inspecting encryption settings on things like S3 buckets, databases, and the disks attached to your virtual machines.
- Logging and Monitoring: Verifying that services for activity logging and threat detection are actually turned on and configured properly across all your critical assets.
Phase 3: Vulnerability Identification
Once you've got all that evidence, the real analysis begins. In this phase, you start connecting the dots, correlating all the data you’ve collected to pinpoint specific vulnerabilities, misconfigurations, and compliance gaps. This is where your team's expertise really shines, as they piece together seemingly unrelated bits of information to uncover potential attack paths.
For instance, your analysis might show an IAM role with overly generous permissions (one piece of evidence) that’s attached to a publicly accessible virtual machine (another piece of evidence). On their own, neither of these might seem like a huge deal. But together? That’s a massive vulnerability. An attacker who compromises that machine could use those permissions to move laterally throughout your entire cloud environment.
This process involves comparing the current state of your environment against the frameworks you defined back in the planning phase. This is where automated tools become your best friend. They can scan thousands of settings against standards like the CIS Benchmarks in minutes, instantly flagging anything that deviates from the baseline.
Phase 4: Reporting and Remediation
This final phase is where all the hard work pays off. A great report does more than just list a bunch of findings—it tells a story. It needs to clearly explain the risks you found, put them in the context of business impact, and provide concrete, actionable steps for fixing them.
Every finding should be prioritized. You have to weigh how easy it is to exploit against the potential damage it could cause. A public S3 bucket with sensitive customer data? That goes straight to the top of the list. A minor logging misconfiguration on a dev server, on the other hand, can probably wait.
Remember to tailor the report to your audience. The executive summary gives leadership the high-level picture of the security posture and the biggest risks. The detailed technical sections give engineers the exact, step-by-step instructions they need to fix each problem. And the assessment isn't really "done" when you hand over the report. It's done when the critical findings have been fixed and you've verified the remediation, completing the cycle and making the organization genuinely more secure.
Using Automation to Streamline Your Assessments
Trying to manually assess a cloud environment is like trying to take a perfect, still photograph of a river. By the time you develop the picture, the river has already changed. Cloud resources, permissions, and configurations shift constantly, making manual checks outdated almost the moment they’re completed. They're slow, riddled with potential for human error, and just can't keep up.
This is where automation completely changes the game. Modern security tools don't just take a single snapshot; they provide a live video feed of your security posture. They continuously scan your cloud environment, flagging misconfigurations and vulnerabilities in real time.
The Power of AI in Compliance Mapping
One of the biggest time sinks in any assessment is the painstaking process of mapping your security controls to dozens of requirements across different compliance frameworks. It's tedious, complex, and exactly the kind of task that's perfect for AI.
AI-powered platforms can ingest all your security policies, architectural diagrams, and procedural documents. From there, they automatically cross-reference everything against dense standards like ISO 27001 or NIST.
Automation injects speed and consistency into every one of these stages, turning what was once a long, linear project into a continuous, repeatable cycle.
By automating evidence collection and control mapping, you free up your security team to do what they do best. Instead of spending their days chasing down log files and screenshots, they can focus on analyzing genuine risks and designing stronger defenses.
The benefits go beyond just speed; accuracy gets a major boost, too. An AI can spot subtle gaps and inconsistencies that a human analyst might easily overlook. It can then provide precise citations, linking a specific weakness directly back to a clause in a compliance standard. The end result is audit-ready reporting that’s generated in a fraction of the time. You can learn more about how to use compliance assessment software to make this happen.
From Data Collection to Actionable Insights
AI-powered gap analysis tools are built to accelerate this entire workflow. They act as a central hub where your team can collaborate on findings, assign and track remediation tasks, and keep a clean, transparent chain of evidence ready for auditors.
These platforms transform mountains of messy documentation into a clear, actionable security dashboard that gives you an evidence-backed view of your compliance status.
Instead of your team spending weeks sifting through documents, they get instant, verifiable answers to their questions. This technology doesn't replace human expertise; it enhances it. It lets your experts make faster, better-informed decisions, freeing them from the grind of manual evidence gathering so they can focus on what really matters: reducing risk and building a more secure cloud. This isn't some far-off idea anymore; it's a practical, essential tool for modern cloud security assessments.
Prioritizing Findings and Measuring Success
Getting a cloud security assessment report back isn't the finish line—it's the starting gun. The real value comes from turning those findings into concrete actions that actually make your security posture better. If you don't have a solid plan for prioritizing and fixing what you find, that detailed report is just going to sit there collecting digital dust.
The first job is to triage the findings. Let's be honest, not all vulnerabilities are created equal. A publicly exposed S3 bucket packed with sensitive customer data is a full-blown emergency. A minor logging misconfiguration on a dev server? Not so much. It all comes down to context—you have to weigh how easily a weakness could be exploited against the damage it could do to the business.
From Findings to Actionable Fixes
To cut through the noise, most teams pull out a risk matrix. It’s a straightforward way to plot out findings based on their severity and how likely they are to happen. This ensures you're tackling the most dangerous stuff first—the issues with the highest probability and the worst potential consequences.
So, what usually lands at the top of the "fix now" list?
- Overly Permissive IAM Roles: These are a goldmine for attackers. They offer a direct route to escalating privileges and moving around freely inside your cloud environment.
- Publicly Accessible Storage: An unsecured S3 bucket or Azure blob is one of the oldest, and still most common, ways massive data breaches happen.
- Missing Data Encryption: Leaving sensitive data unencrypted in databases or storage is like leaving the vault door wide open. If someone gets in, they get everything.
- Unrestricted Network Access: Security groups that allow traffic from any IP address (0.0.0.0/0) on sensitive ports are basically a "welcome" sign for attackers.
For every finding, the fix needs to be crystal clear. "Fix the IAM role" is useless. What you need is something like, "Remove the s3:DeleteObject permission from the 'WebApp-ReadOnly' role and apply a more restrictive policy." That kind of specificity ensures the right fix gets done quickly and correctly.
Tracking Progress with Security KPIs
Once you start rolling out fixes, how do you know if it's actually working? This is where Key Performance Indicators (KPIs) come into play. When you track the right metrics, you can tell a story of continuous improvement, backed by real data.
Measuring success is how you build a mature security program. It shows the value of your work to leadership, helps justify your budget, and turns security from a simple cost into something that enables the business to run safely.
Here are a few key metrics worth monitoring:
- Mean Time to Remediate (MTTR): This is the average time it takes your team to fix a vulnerability once it’s been discovered. If your MTTR is steadily going down, it’s a great sign your remediation process is getting sharper.
- Reduction in Critical Findings: Simply count the number of high-severity findings you have from one assessment to the next. A downward trend is a powerful sign that your overall security foundation is getting stronger.
- Compliance Adherence Percentage: If you’re tied to standards like ISO 27001 or PCI DSS, track what percentage of controls you're fully compliant with. This gives you a clear snapshot of how ready you are for an audit. To learn more about this process, you can explore our guide to conducting a comprehensive cybersecurity risk assessment.
By prioritizing findings with a clear head and tracking these KPIs, you close the loop on the assessment. You make sure every discovery leads to a stronger, more resilient cloud environment.
Common Questions About Cloud Security Assessments
Diving into cloud security assessments for the first time? It's natural to have questions. Getting the fundamentals right from the start is key to making the whole process worthwhile, not just a box-ticking exercise. Let's clear up a few of the most common questions we hear.
How Often Should We Conduct an Assessment?
There's no single magic number, but a good rule of thumb is to conduct a full-scale, deep-dive assessment at least annually. That gives you a solid, comprehensive baseline of your security posture.
However, the cloud moves fast, and so should your security reviews. For a more dynamic approach, supplement that annual assessment with continuous automated scanning and more focused reviews every quarter.
Certain events should also act as immediate triggers for an assessment. You don't want to wait a year if something big changes. Plan for a review after:
- A major overhaul of your cloud architecture.
- Rolling out a new critical application.
- A merger or acquisition that brings new, unknown infrastructure into the fold.
This rhythm ensures your security posture evolves right alongside your business.
What Is the Difference Between an Assessment and a Scan?
This is a big one, and it's easy to confuse the two. A vulnerability scan is a tactical, automated process. It’s like running a spell-checker on a document—it’s great at finding known, common mistakes from a predefined list. It's a crucial piece of security hygiene, but it's only one piece.
A cloud security assessment is the whole strategic review. It’s the human editor who reads the document for context, tone, and logic. An assessment looks at the big picture—your architecture, access controls, data policies, and compliance gaps—to find risks a simple scan would never see.
An assessment gives you the "why" behind the vulnerabilities and helps you understand the true business risk, not just a list of technical flaws.
Should We Use In-House Teams or a Third Party?
The best answer is usually both. It's not an either-or decision; it's about playing to strengths.
Your in-house team is on the front lines every day. They should own the continuous monitoring and daily security work, using automated tools to keep things in check. This builds and maintains internal expertise.
But bringing in a specialized third-party firm, perhaps annually, offers a fresh, unbiased perspective. An external team isn't influenced by internal politics or historical decisions and can spot things your team might have overlooked. Plus, for many compliance frameworks and certifications, that independent validation is non-negotiable.
Ready to transform your lengthy compliance documents into clear, audit-ready reports? AI Gap Analysis uses AI to read your evidence, map it to frameworks like ISO 27001, and pinpoint gaps instantly. Get started today and streamline your next assessment. Find out more about AI Gap Analysis.