February 13, 2026
cmmc level 2nist 800-171cui protectiondod compliancec3pao assessment
A Practical Guide to CMMC Level 2 Compliance
Master CMMC Level 2 with our step-by-step guide. Learn the 110 controls, navigate the assessment process, and implement a roadmap to protect CUI.
21 min readAI Gap Analysis
If you're a Department of Defense (DoD) contractor, you've undoubtedly heard about CMMC Level 2. But what does it really mean for your business? Simply put, if you handle Controlled Unclassified Information (CUI), CMMC Level 2 is your required standard for cybersecurity. It’s not just a suggestion—it's a gatekeeper for winning and keeping contracts.
At its core, Level 2 means you must implement all 110 security controls found in NIST SP 800-171 and, crucially, pass an official assessment conducted by a third-party auditor. Without that certification, contracts involving sensitive government data are off the table.
Decoding CMMC Level 2 and Its Strategic Importance
Think of CMMC Level 2 as the digital equivalent of a security clearance for your entire company. Just as an individual needs clearance to handle classified documents, your organization needs this certification to be entrusted with CUI. It’s how the DoD verifies that every single partner in the Defense Industrial Base (DIB) supply chain is strong enough to protect sensitive information from ever-present cyber threats.
This is a massive change from how things used to be. For years, many contractors could simply self-attest that their cybersecurity was up to snuff. With CMMC Level 2, that era is over. Now, you need undeniable proof.
The Shift from Trust to Verification
The entire CMMC Level 2 framework is built on the foundation of NIST SP 800-171. The 110 controls themselves aren't new, but the way they are enforced absolutely is. The DoD has officially moved from a "trust us, we're secure" model to a "prove it" mandate. This single change turns compliance from a simple IT project into a critical business objective.
This transition highlights a few non-negotiable realities for all contractors:
- Compliance is mandatory: It's no longer optional. If the contract involves CUI, you need the certification.
- Evidence is everything: You have to be ready to demonstrate that all 110 controls are not just in place but are actively working.
- Third-party validation is required: Your security program will be audited by an accredited CMMC Third-Party Assessment Organization (C3PAO).
CMMC 2.0 Levels at a Glance
To fully grasp where Level 2 fits, it helps to see it alongside the other tiers. This table breaks down the key differences between the three levels of CMMC 2.0.
| Level | Title | Required Practices | Assessment Type |
|---|---|---|---|
| Level 1 | Foundational | 17 Practices (from FAR 52.204-21) | Annual Self-Assessment |
| Level 2 | Advanced | 110 Practices (aligned with NIST SP 800-171) | Triennial Third-Party Assessment |
| Level 3 | Expert | 110+ Practices (based on NIST SP 800-172) | Triennial Government-Led Assessment |
As you can see, Level 2 represents a significant step up from the basic self-assessment of Level 1 and is the new standard for protecting CUI.
Why It Matters Beyond Just Winning Contracts
Achieving CMMC Level 2 certification is about more than checking a box on a government form; it’s a powerful competitive advantage. It sends a clear signal to prime contractors and the DoD that your company is a trustworthy, secure partner. In an industry where a single data breach can have national security consequences, that kind of verified trust is invaluable.
The real point of CMMC Level 2 isn’t just about having security controls. It's about proving they are consistently managed, effective, and operational. It forces cybersecurity to evolve from a background IT task into a core business function that directly protects your revenue and reputation.
Ultimately, preparing for a CMMC Level 2 assessment pushes you to build a truly resilient cybersecurity program. It compels your organization to move beyond basic firewalls and antivirus software and adopt a mature, well-documented, and auditable security posture. This effort not only secures your government contracts but also hardens your defenses against all kinds of cyber threats, protecting your entire business in the process.
A Practical Look at the 110 CMMC Level 2 Security Controls

The core of CMMC Level 2 is its set of 110 security controls. Staring at a list that long can feel intimidating, but these controls aren’t just arbitrary busywork. They map directly to NIST SP 800-171, a battle-tested framework for protecting sensitive government information.
Don't think of it as a random checklist. Instead, view it as a complete blueprint for building a digital fortress around your Controlled Unclassified Information (CUI). The smartest way to tackle this is by understanding the why behind the controls, not just memorizing the list. They’re logically grouped into 14 families, which we can organize into three practical themes to make things more manageable.
Theme 1: Controlling Digital Access
The first and most important theme is all about managing who gets to touch your systems and data. Think of your company network like a secure building—you wouldn't let just anyone wander in and start opening filing cabinets. The same logic applies to your digital assets.
Two key control families lay the groundwork here:
- Access Control (AC): This is your building's keycard system. It determines who is allowed in, which doors they can open, and what they're permitted to do once inside. These controls ensure users only have access to the specific information their job requires—a concept called the "principle of least privilege."
- Identification and Authentication (IA): This is the security guard at the front desk checking IDs to make sure your keycard actually belongs to you. It's about proving identity with tools like passwords, multi-factor authentication (MFA), and other methods before anyone gets on the network.
Getting these controls right is your first line of defense. Our guide on building an effective access control policy can help you set these foundational rules.
Theme 2: Strengthening Your Defenses
Once you’ve locked the doors, the next step is to build strong walls and a good surveillance system. This theme focuses on creating a proactive security posture, moving beyond just reacting to problems after the fact. It’s all about continuous monitoring, smart planning, and hardening your systems against attack.
This theme pulls from several control families:
- Audit and Accountability (AU): This is like having security cameras everywhere. You’re creating a detailed log of all activity on your network so if something bad happens, you have the digital footage to figure out exactly what went down.
- Incident Response (IR): You need a fire drill plan. This is your documented procedure for what to do when a breach occurs, covering everything from containment and eradication to recovery, all to minimize the damage.
- Risk Management (RM): This is where you actively hunt for potential security risks to your systems and data, figure out how bad they could be, and then put measures in place to reduce those risks.
- Security Assessment (SA): You have to kick the tires regularly. This involves testing your security controls to find weaknesses before an attacker does.
At its heart, CMMC Level 2 is about showing you have a mature security program. It’s not enough to just install security software; you must prove it’s configured correctly, monitored constantly, and tied into a documented risk management strategy.
Theme 3: Protecting Your Systems and Information
This final theme gets into the nitty-gritty of protecting the technical integrity of your systems and the CUI they hold. It's about making sure your information is accurate, available when you need it, and safe from being changed or destroyed by the wrong people—whether it’s sitting on a server or flying across the network.
The key control families in this theme include:
- System and Information Integrity (SI): This is often one of the toughest areas for small businesses. It involves everything from protecting systems against malware to monitoring for unauthorized changes, all to ensure your data remains trustworthy.
- Configuration Management (CM): This practice establishes and maintains a consistent, secure setup for all your hardware and software. It prevents security gaps that pop up when systems are configured on the fly or inconsistently.
- Media Protection (MP): Here, you're securely managing any physical or digital media containing CUI—from USB drives to backup tapes—through its entire life, from creation to secure disposal.
By grouping the 110 controls into these three themes—Controlling Access, Strengthening Defenses, and Protecting Systems—you can build a clear strategy. This approach transforms the path to CMMC Level 2 compliance from a daunting checklist into a logical, layered, and truly defensible cybersecurity program.
Getting Through the CMMC Level 2 Assessment
Knowing the 110 controls is one thing. Being able to prove you’re doing them is a completely different ballgame. This is the heart of the CMMC Level 2 assessment process—it’s not about what you say you do, but what you can show you do. The days of simply checking a box and attesting to your own security are gone. Evidence is now king.
For most companies handling Controlled Unclassified Information (CUI), CMMC Level 2 demands a formal assessment every three years. This isn't just a friendly check-in; it's a full-blown audit conducted by an accredited CMMC Third-Party Assessment Organization, or C3PAO. Think of them as independent inspectors who will scrutinize your systems, comb through your paperwork, and interview your team to confirm every single one of those 110 controls is working as intended.
Now, there's a small wrinkle here. A select few Level 2 contracts might not require this intense third-party audit. Instead, they may only ask for an annual self-assessment where you grade your own compliance and report the scores to the DoD. The bottom line? Always, always check your contract to see which path you need to follow.
Why Documentation and Evidence Are Your Best Friends
Getting ready for a Level 2 assessment means you need tangible proof for every security requirement. When an auditor asks how you control access to sensitive files, a simple "we have a process for that" won't cut it. You need to pull out the documented policy, show them the system logs that prove it's enforced, and produce the training records that confirm your team knows the rules.
This is where a lot of businesses stumble. They might have great technical security in place—firewalls, multi-factor authentication, the works—but they're missing the paper trail to back it all up.
The unofficial motto of any CMMC Level 2 assessment should be: If it isn’t written down, it never happened. Your evidence needs to tell a story that's so clear and consistent an auditor can easily follow along and check every box.
This documentation effort is a huge part of why compliance gets expensive. For a small business, the total price tag to get to Level 2 can run anywhere from $50,000 to over $400,000, from implementation to the final audit. That massive range often boils down to the sheer work involved in creating a rock-solid System Security Plan (SSP) and gathering evidence for all 320 individual assessment objectives. You can get a deeper dive into the predicted costs and challenges of CMMC on strikegraph.com.
Your Compliance Story: The System Security Plan (SSP)
If there's one document that matters more than any other on your CMMC journey, it's the System Security Plan (SSP). This isn't just another policy gathering dust on a server. It's the central playbook for your entire cybersecurity program. The SSP is where you describe, in painstaking detail, how your company meets every single one of the 110 security controls.
A truly solid SSP will include things like:
- A detailed network diagram that clearly marks the boundary where CUI lives.
- An inventory of your hardware, software, and key security personnel.
- A clear, plain-English explanation for how each control is met (the what, how, and why).
Think of the SSP as the script your C3PAO auditor will be working from. A well-crafted SSP not only makes their job easier but also screams that your organization is mature and serious about security.
Your Strategic Roadmap: The Plan of Action & Milestones (POA&M)
Let's be real: no company is perfect, and the DoD knows it. If you find security gaps during your own internal review, you're expected to document them in a Plan of Action & Milestones (POA&M). This is your official roadmap for fixing what's broken.
A POA&M isn't a get-out-of-jail-free card for ignoring major security flaws. What it does do is show an auditor that you have a formal process for finding, tracking, and resolving weaknesses. For every gap you list, your POA&M needs to detail:
- Exactly what the weakness is.
- What resources (people, money, tools) you need to fix it.
- The key milestones you'll hit along the way.
- A firm date for when it will be completed.
Together, the SSP and the POA&M give a complete picture of your security posture—where you're strong, and where you have a concrete plan to get better. Mastering these two documents is your key to getting through the CMMC Level 2 assessment and keeping your place in the Defense Industrial Base.
A Step-By-Step Roadmap for CMMC Level 2 Implementation
Getting ready for a CMMC Level 2 assessment can feel overwhelming, but it's much more manageable when you break it down into a clear, phased roadmap. This isn't about a mad dash to the finish line; it’s a deliberate process of maturing your security program until it’s not just effective, but provable.
By following a logical sequence, you can build momentum, measure your progress, and make sure nothing critical slips through the cracks. Let's walk through the five core phases that will take you from initial planning to being fully prepared for your assessment.
Phase 1: Define Your CUI Scope
Before you can protect anything, you have to know exactly what you’re protecting and where it lives. This first phase is all about scoping—drawing a clear boundary around every system, person, and process that touches Controlled Unclassified Information (CUI).
Think of it like building a fence. You need to map out the entire perimeter. This means:
- Finding the data: Where is CUI stored, processed, or transmitted? Comb through file servers, cloud accounts, email inboxes, and local machines.
- Mapping the systems: Which applications, network devices, and servers interact with that CUI?
- Identifying people and processes: Who needs access to CUI to do their jobs, and what business workflows involve it?
Getting the scope wrong is one of the most common and expensive mistakes a company can make. If it’s too narrow, you leave CUI exposed and are guaranteed to fail your audit. If it’s too broad, you'll waste a ton of time and money applying unnecessary controls to out-of-scope systems.
This initial work is the foundation for the entire assessment process.
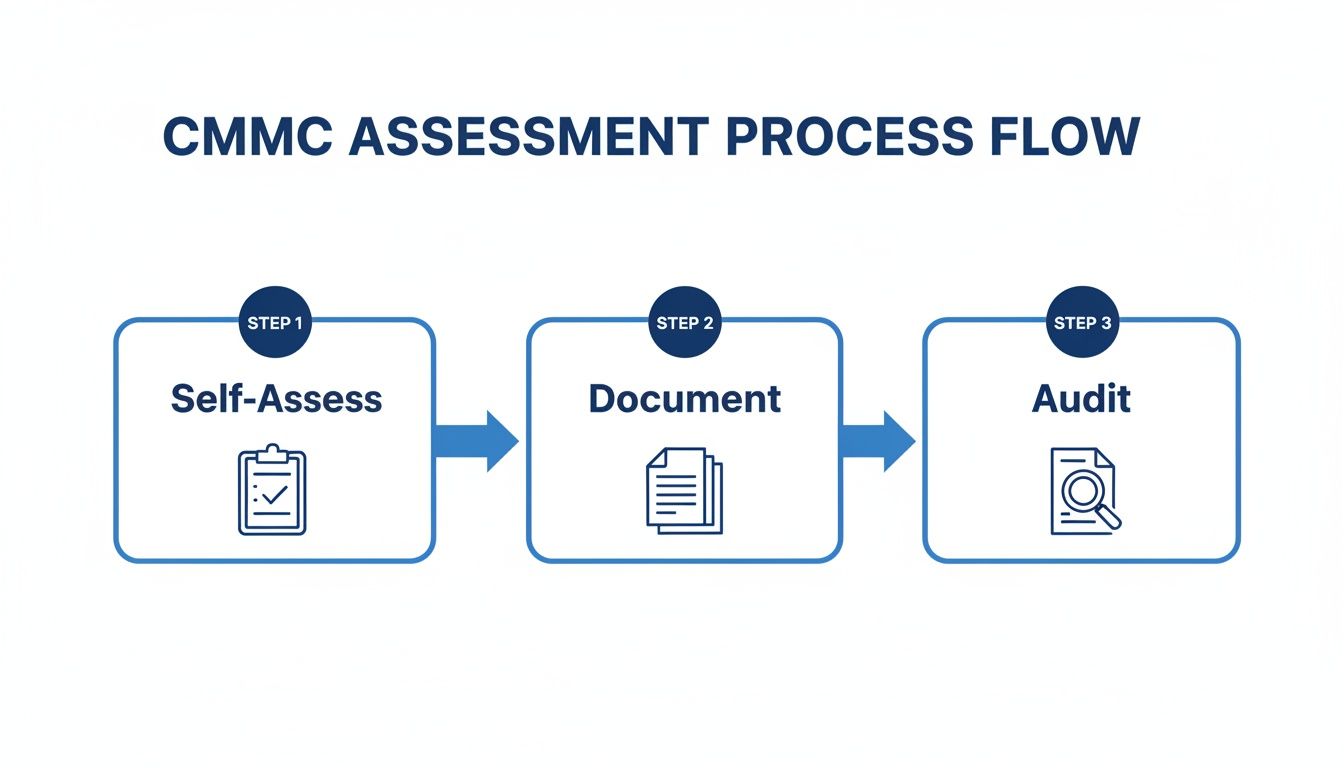
As you can see, a successful third-party audit is built on solid internal assessment and documentation. It all starts here.
Phase 2: Perform a Gap Analysis
Once you know what's in scope, it's time for a reality check. How does your current security posture stack up against the 110 controls required for CMMC Level 2? This is the gap analysis, where you meticulously compare what you’re actually doing with what you’re supposed to be doing.
This step is critical for understanding the true scale of the project ahead. You need to be brutally honest with yourself. For each of the 110 controls, you have to determine if you fully meet it, partially meet it, or don't meet it at all. Assumptions won't cut it; you need to start gathering the evidence to back up your assessment. For a deeper dive into this, check out our guide on the gap assessment process.
Phase 3: Build Your Remediation Plan and POA&M
The results from your gap analysis become the direct input for this phase: creating a remediation plan. This is your project plan for closing every single identified security gap. It needs to be detailed, actionable, and prioritized based on risk and level of effort.
This is also where you create your formal Plan of Action & Milestones (POA&M). A POA&M is a living document that lists every unmet control and details the specific steps, resources, and timelines needed to get it to a "met" state.
A well-maintained POA&M is a sign of a mature security program. It proves to an auditor that you have a formal process for tracking and resolving weaknesses, which is exactly what they want to see.
Phase 4: Implement Controls and Document Everything
Now for the heavy lifting. This phase is all about executing your plan—deploying new software, reconfiguring firewalls, writing new policies, and training your team. It’s often the longest and most resource-intensive part of the journey.
As you implement each control, one word should be top of mind: documentation.
From an auditor's perspective, if it isn’t documented, it never happened. For every single control, you need to be creating and collecting the evidence that proves you've implemented it correctly. This means policies, procedures, screenshots of system settings, security logs, and training completion records.
Phase 5: Prepare for Your Final Assessment
Once all your remediation tasks are complete and your POA&M is clear (or only has a few minor, low-risk items left), it’s time to prepare for the final assessment with your C3PAO. Think of this as the final dress rehearsal.
You’ll want to conduct one last internal review, organize all your evidence into a clean, easy-to-navigate package, and prep your team for interviews with the auditors. Your goal is to make it as easy as possible for the auditor to see that your documentation tells a clear, complete, and compelling story of compliance.
How AI Is Changing the Game for CMMC Gap Analysis
Anyone who has prepared for a CMMC Level 2 assessment knows the grind. Traditionally, it’s a manual, painstaking process. Your team is buried for hundreds of hours, sifting through mountains of policy documents, system security plans (SSPs), and standard operating procedures. The goal? To manually connect the dots between what's written in those documents and the 110 required CMMC controls.
It’s slow, it’s expensive, and honestly, it’s a recipe for human error. One missed piece of evidence or a slightly misinterpreted control can mean a failed audit, which puts valuable DoD contracts on the line. For small and medium-sized businesses, the sheer volume of work can feel like an insurmountable wall.
Finding and Mapping Evidence Without the Manual Drudgery
This is where things are getting interesting. Modern platforms are bringing AI into the fold to automate the most grueling parts of a gap analysis. Instead of having someone read every single page, these tools let you upload all your compliance documentation—network diagrams, incident response plans, employee handbooks, you name it—into a secure system.
From there, an AI agent gets to work. It reads and comprehends the content, intelligently mapping your existing language directly to the specific CMMC Level 2 requirements.
Think of it this way: AI takes a chaotic pile of documents and turns it into an organized, easy-to-understand compliance dashboard. It doesn't replace the need for an expert's judgment; it just gives them a massive head start by doing all the heavy lifting of finding and organizing the proof.
This automated mapping instantly shows you where your documentation is strong and, more critically, where it’s thin or missing entirely. It doesn't just say "you have a gap"—it flags the specific control and often points to the exact page and paragraph in your source files, making verification a breeze.
The AI-powered dashboard below is a great example of how this works. It visualizes how evidence is automatically tied to controls, giving you immediate clarity.
This kind of visualization turns a daunting checklist into an interactive workspace. Your team can see your compliance posture in real-time.
From Document Chaos to Audit-Ready in Record Time
The speed and accuracy you get with AI is a total game-changer for CMMC prep. A task that used to take weeks of tedious cross-referencing can now be done in a few hours, sometimes even minutes. This drastically shrinks the time it takes to go from your initial internal review to actually fixing the problems.
Here’s how this new approach gets you audit-ready faster:
- Instant Mapping: The AI automatically connects sentences and paragraphs in your documents to the 110 CMMC Level 2 controls.
- Precise Citations: It gives you the exact page numbers and deep links, so you can click and verify the evidence on the spot.
- Clear Gap Identification: The system immediately pinpoints which controls have weak or nonexistent documentation.
- Better Collaboration: Everyone can work from the same dashboard, making it easy to assign tasks and track progress on closing gaps.
This entire process brings the rigor of a formal CMMC assessment into your preparation phase but slashes the time investment. Platforms that can ingest PDFs and map them to the 110 controls are accelerating the journey from document chaos to audit-ready findings. As we dive deeper into in our article on AI for regulatory compliance, this technology is reshaping how companies tackle complex frameworks. With some tools now available for a low monthly cost, an AI-driven gap analysis isn't just for large enterprises anymore—it's making CMMC Level 2 compliance a much more achievable goal for everyone.
Common CMMC Level 2 Mistakes to Avoid
Getting to CMMC Level 2 is a tricky process, and it's easy to see even the most well-prepared companies hit a snag. Knowing where others have gone wrong gives you a huge advantage, saving you from headaches, wasted money, and maddening delays down the road. Honestly, learning from others' mistakes is one of the best ways to get your own compliance journey right the first time.
Most of these slip-ups come from a basic misunderstanding of what assessors are actually looking for. It’s less about having the fanciest new technology and more about being able to prove you have a security program that is mature, well-documented, and consistently followed.
Treating Compliance as a One-Time Project
By far, the most common error I see is treating CMMC Level 2 like a final exam. Companies grind for months to get ready for the assessment, pass it, and then let all their hard work and documentation collect digital dust. But CMMC isn't a one-and-done deal; it’s an ongoing commitment.
Security controls need constant attention, logs have to be reviewed regularly, and your System Security Plan (SSP) must be a living, breathing document that evolves as your environment changes. An assessor needs to see proof of continuous security management, not just a perfect snapshot from a single day.
CMMC certification isn’t a trophy you put on a shelf. It's a garden you have to tend to continuously. If you forget to weed, water, and prune your security program, you can guarantee it won't pass the next inspection.
Underestimating Evidence Requirements
It’s a disastrous assumption to think that just because you have a security tool, you have the evidence to prove it's working. For example, you might have a top-of-the-line firewall, but can you pull up the logs to show you’re reviewing its rule sets every quarter? You might have an access control policy, but can you produce the signed forms and system audit trails proving you follow it every single time someone leaves the company?
Recent assessments have revealed a harsh truth: many defense contractors think they're ready, but they're not. They often fail because their evidence is thin and their SSPs are incomplete, leading to failed audits and putting valuable contracts on the line. You can read more about what assessors are finding in the field in these 2025 assessment findings on strikegraph.com.
Common Evidence Gaps to Watch For
To keep this from happening to you, get laser-focused on generating and collecting proof for every single one of the 110 controls. Pay close attention to these areas where people often fall short:
- Maintenance Records: Can you show proof that you perform regular maintenance on key systems, just like your policy says you do?
- Visitor Logs: Do you have complete physical and digital logs tracking who comes and goes from facilities and systems where CUI is stored or processed?
- Incident Response Tests: Where are the records from your tabletop exercises or mock drills? You need to show your response plan actually works and your team knows what to do.
- Employee Training Completion: You'll need certificates or signed acknowledgments proving that every single person has finished their annual security awareness training.
By getting ahead of these common stumbles, you can build a compliance strategy that's not just effective, but resilient. Avoiding these mistakes turns the whole CMMC Level 2 process from a nightmare into a predictable part of doing business.
Your CMMC Level 2 Questions, Answered
Getting ready for CMMC Level 2 brings up a lot of questions. Let's tackle some of the most common ones we hear from defense contractors so you can plan your compliance journey with confidence.
How Long Does It Take to Get Certified?
This is probably the most common question, and the honest answer is: it depends entirely on where you're starting from. Most companies should plan for a 6 to 18-month journey from their first gap assessment to being truly audit-ready.
The timeline really hinges on a few key factors: how complex your network is, how much CUI you handle, and whether your team can dedicate consistent time to the effort. If your organization is new to cybersecurity frameworks, you're looking at a much longer runway than a company that has already been working with NIST standards.
Can We Use Cloud Services Like AWS or Azure?
Absolutely, but you have to be careful. Using the cloud introduces what’s known as a shared responsibility model. The cloud provider, like Amazon Web Services (AWS) or Microsoft Azure, is responsible for the security of the cloud, but you are always responsible for security in the cloud. That means your data and how you configure your services are on you.
A critical point for handling CUI: you can't just use the standard commercial versions of these cloud platforms. You'll need to operate within government-specific environments, such as AWS GovCloud or Microsoft Azure Government (including GCC High), which are built to meet the rigorous security demands of federal data.
What's the Difference Between a Self-Assessment and a C3PAO Assessment?
The main difference boils down to who is doing the checking and how much weight the results carry.
- Self-Assessment: Think of this as an internal health check. Your own team goes through the 110 controls and scores your compliance. For some CMMC Level 2 contracts, an annual self-assessment is all that's required.
- C3PAO Assessment: This is the formal, third-party audit. A certified CMMC Third-Party Assessment Organization (C3PAO) comes in to independently verify your compliance. This rigorous process is mandatory for most contracts involving critical CUI and, if you pass, earns you a three-year certification.
Do We Really Need to Meet All 110 Controls?
In a perfect world, yes. But the DoD knows that perfection isn't always realistic on day one. If you have a few controls that aren't fully buttoned up by your assessment date, you can place them on a Plan of Action & Milestones (POA&M).
This document serves as a formal roadmap, showing the auditor that you've identified the gap and have a clear, time-bound plan to fix it. Be warned, though: the most heavily weighted, critical controls can't be on a POA&M, and there's a strict limit on how many open items you can have.
You can jumpstart your compliance process by automating the most tedious part of any gap analysis. Our AI Gap Analysis tool lets you upload your existing policies and procedures, and our AI agent will instantly map that evidence against the 110 CMMC Level 2 controls. It finds your gaps in minutes, not weeks, so you can get on the path to being audit-ready. See how it works at https://ai-gap-analysis.com.