February 9, 2026
iso 27001 requirementsisms frameworkannex a controlsinformation securitycompliance audit
A Practical Guide to ISO 27001 Requirements
Master the ISO 27001 requirements with our guide. We break down mandatory clauses, Annex A controls, and documentation for a successful audit.
24 min readAI Gap Analysis
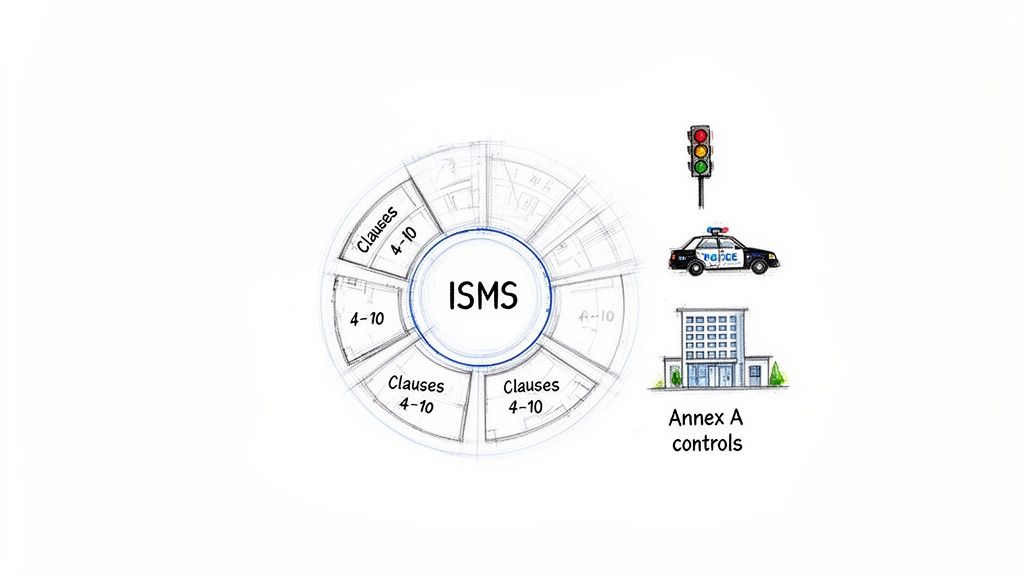
At its heart, ISO 27001 is broken down into two distinct but interconnected parts. First, you have the mandatory management system clauses (Clauses 4-10), which are all about how you build and operate a robust Information Security Management System (ISMS). Then, there's a list of 93 potential security controls in Annex A, which detail what specific protections you can put in place.
When you bring these two pieces together, you get a powerful, strategic framework for systematically handling your organization's information security risks.
Understanding the Blueprint for Your Security Program
Think of it like this: if you were going to build a brand-new city from scratch, you wouldn't just start laying down asphalt and putting up buildings wherever you felt like it. You'd need a master plan—a blueprint—to make sure everything works together safely and efficiently. ISO 27001 is that exact blueprint for your company's data security.
This is why the standard isn't just a simple to-do list of technical fixes. Instead, the ISO 27001 requirements are designed to help you create a complete management system—your Information Security Management System (ISMS). This ISMS is essentially your documented, structured approach for identifying, evaluating, and ultimately treating information security risks.
The Two Pillars of ISO 27001
The entire standard really rests on two fundamental components that work in tandem. Getting a handle on their distinct roles is the first real step on the path to compliance. We cover this in more detail in our guide on what is ISO 27001 compliance.
- Mandatory Clauses (4-10): These are the non-negotiable "zoning laws" for your security city. They lay out the structure and rules for how your ISMS must operate, touching on everything from leadership commitment and risk assessment to ongoing improvement. You must meet these for certification.
- Annex A Controls: This is your catalog of potential safety features—things like traffic lights, a police force, or secure building codes. Annex A provides a menu of 93 security controls, but the key is that you only implement the ones that make sense for the specific risks you've identified.
The real goal of ISO 27001 isn't to make you implement every security measure under the sun. It's about forcing you to make smart, deliberate, risk-based decisions on how to best protect your information and then prove you're sticking to the plan you created.
This systematic approach is precisely why ISO 27001 adoption is surging. In fact, a striking 81% of organizations now report they are either certified or plan to be by 2025, a huge jump from just 67% in 2024. This isn't surprising, especially when you consider that 43% of all cyber attacks are aimed squarely at small and medium-sized businesses that can't afford a major breach.
To help clarify the structure, here’s a quick breakdown of the standard's core components.
Core Components of ISO 27001 at a Glance
| Component | Clause/Section | Purpose |
|---|---|---|
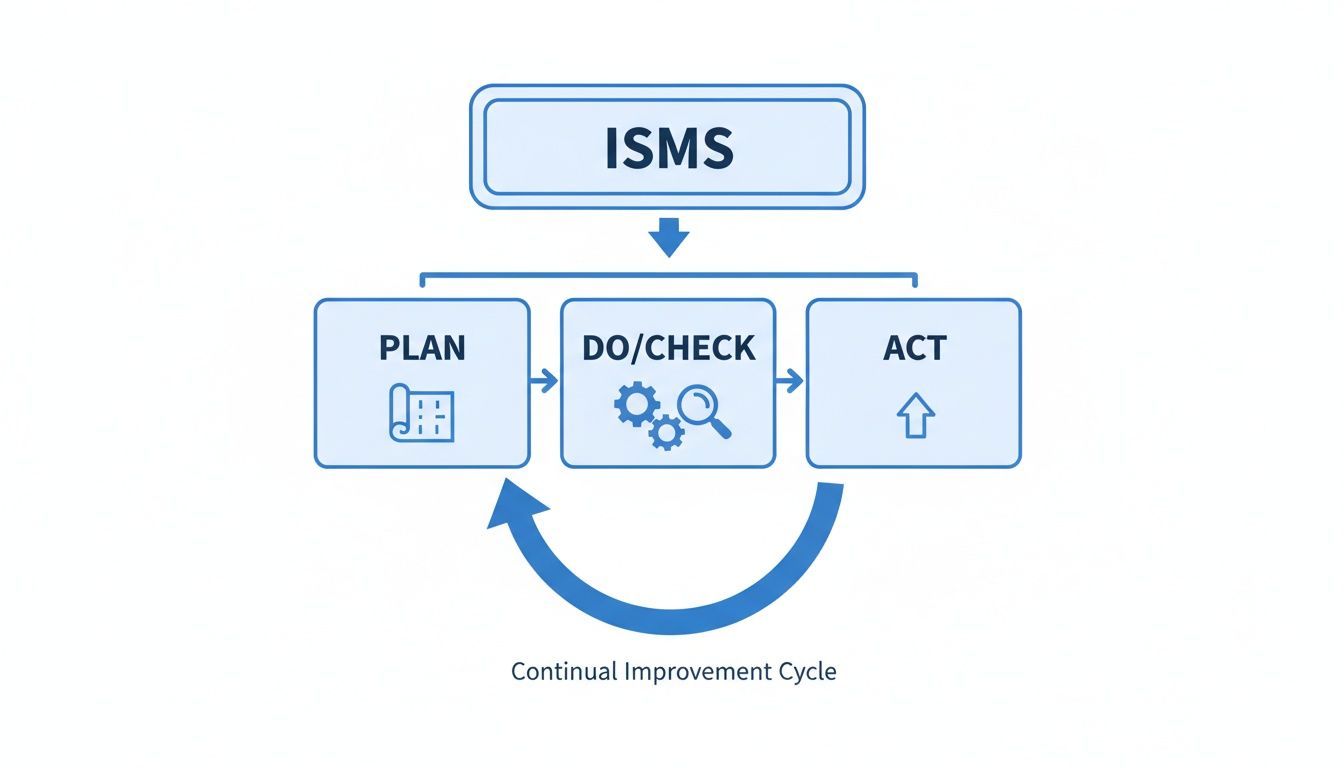
| ISMS Management System | Clauses 4–10 | Establishes the mandatory "Plan-Do-Check-Act" framework for managing information security. |
| Security Controls | Annex A | Provides a comprehensive list of 93 potential security controls to treat identified risks. |
Understanding this division is crucial. The clauses tell you how to manage security systematically, while Annex A gives you the tools to actually do it.
The Core of Your ISMS: A Clause-by-Clause Breakdown
While everyone talks about the Annex A controls, the real heart of ISO 27001 is found in Clauses 4 through 10. These are the mandatory requirements that give your Information Security Management System (ISMS) its structure, its purpose, and its power. Think of them less as a checklist and more as the operational blueprint for your entire security program.
These clauses are the engine, not just the paint job. They force you to build a system that manages security strategically, rather than just plugging in technical fixes and hoping for the best. Let’s walk through what each one is really asking for and the kind of proof auditors will want to see.
Clause 4: Understanding the Organization and Its Context
Before you can protect your assets, you have to know what you're working with. Clause 4 is all about defining the "why" behind your ISMS. This isn't just an internal thought exercise; it's about looking at your organization from the outside-in and the inside-out.
First, you need to identify your interested parties. Who cares about your information security? This list is longer than you think: customers, employees, regulators, investors, and even your key suppliers. What do they expect from you? A customer expects their personal data to be kept private, while a regulator demands you comply with specific laws like GDPR or HIPAA.
The main output here is a clearly defined ISMS scope. This document formally draws a line in the sand, stating exactly which parts of your organization, which products, or which office locations are covered. Get this wrong, and you'll either fail your audit or spend a fortune protecting things that don't need it.
Clause 5: Leadership and Commitment
Let's be blunt: an ISMS without genuine leadership backing is dead on arrival. Clause 5 puts the responsibility for information security right where it belongs—on the shoulders of top management. They can't just sign the checks; they have to be visibly and actively involved.
This clause requires leadership to do three critical things:
- Establish a security policy: This is the high-level "constitution" for security. It sets the tone, direction, and core principles for the entire organization.
- Assign roles and responsibilities: You need a crystal-clear map of who owns what. From the CISO down to the intern, everyone's security duties must be defined.
- Provide necessary resources: An ISMS doesn't run on good intentions. Leadership must commit the budget, people, and tools needed to actually get the job done.
Auditors will look for real evidence here, like board meeting minutes where security is a key agenda item, a formally signed-off policy, and an org chart that clearly outlines security roles.
Clause 6: Planning for the ISMS
With your context set and leadership on board, Clause 6 is where the real strategic work begins. This is all about proactive planning—specifically, getting a handle on your risks and opportunities. The star of the show here is the formal risk assessment.
You have to systematically identify potential threats to your critical information, figure out how likely they are to happen, and what the damage would be if they did. This process culminates in a Risk Treatment Plan, which is your battle plan for handling each major risk. Will you mitigate it with a control, accept it, avoid it, or transfer it (like with insurance)?
Here's the key: Your risk assessment is what connects your security strategy to your security controls. It's the logic that justifies every single control you pick from Annex A, turning your security program from a guessing game into a calculated, evidence-based defense.
Clause 7: Support and Resource Management
An ISMS is run by people, powered by tools, and held together by communication. Clause 7 is all about making sure the underlying support structure is strong enough to hold everything up.
This clause covers the essential, and often overlooked, pillars of a successful program:
- Resources: Having the right infrastructure, software, and tools.
- Competence: Making sure your team has the skills and training to actually perform their security duties effectively.
- Awareness: Running programs to ensure every single employee understands the security policy and their personal responsibility in upholding it.
- Communication: Having clear channels for communicating security issues, updates, and incidents, both internally and to external parties.
- Documented Information: This is about creating and managing all the policies, procedures, and records the standard requires.
Clause 8: Operational Planning and Control
If Clause 6 was the blueprint, Clause 8 is the construction phase. This is where all that planning becomes a reality. You're now expected to implement the processes and controls you laid out in your Risk Treatment Plan.
Put simply, this is the "doing" part of the ISMS. It’s where you roll out the security controls from Annex A that you chose to mitigate your risks. For example, if your risk assessment flagged weak passwords as a high risk, Clause 8 is where you would implement and enforce your new password policy and multi-factor authentication systems.
Clause 9: Performance Evaluation
How do you know if any of this is actually working? You can't just set it and forget it. Clause 9 mandates that you continuously monitor, measure, and evaluate the effectiveness of your ISMS.
There are two primary activities an auditor will check for:
- Internal Audits: You need to conduct your own periodic audits to verify that the ISMS is running as designed and still meets the ISO 27001 requirements.
- Management Reviews: Top management must regularly meet to review the ISMS's performance, look at internal audit results, discuss incidents, and make strategic decisions for improvement.
Clause 10: Continual Improvement
Finally, Clause 10 cements the idea that security is never "done." An ISMS is not a one-time project; it's a living, breathing process.
This clause requires you to have a formal system for handling nonconformities (i.e., when something goes wrong or a control fails) and implementing corrective actions. The goal isn't just to fix the immediate problem, but to analyze the root cause and make changes to prevent it from ever happening again. This creates the crucial feedback loop that allows your ISMS to learn, adapt, and get stronger over time.
Navigating the Annex A Security Controls
If the main clauses of ISO 27001 are the engine of your Information Security Management System (ISMS), think of Annex A as the specialized toolkit. It can look intimidating at first, but it’s really just a comprehensive catalog of potential security measures. Annex A lists 93 security controls you can pick from to tackle the specific risks you uncovered during your risk assessment.
Here's the key: you don't have to implement all 93 controls. Your choices are driven entirely by your risk assessment. This is a core principle of ISO 27001—every security measure you put in place must be a direct response to a real, identified risk. This ensures you're spending your time and money protecting what actually matters to your business.
The whole process is part of a continuous loop, often called the Plan-Do-Check-Act (PDCA) cycle. Planning your risk treatments using Annex A is the foundational step.
To make this list of controls easier to work with, the 2022 version of the standard organizes them into four logical themes.
H3: Organizational Controls
This is the biggest category, with 37 controls that set the overall security governance for your entire company. Think of these as the high-level policies and procedures that establish the "rules of the road" for information security, creating a foundation for everything else.
A few examples really bring this to life:
- Asset Management: This is the classic "you can't protect what you don't know you have." It’s all about creating and maintaining a complete inventory of your information assets—laptops, servers, databases, and even intellectual property.
- Information Security in Supplier Relationships: Your security is often only as strong as your weakest partner. This control forces you to get a handle on the security risks coming from your vendors and suppliers.
- Threat Intelligence: This isn't about waiting for an attack. It's about actively gathering and analyzing information on emerging threats so you can adjust your defenses before you get hit.
These controls are all about setting the strategic direction for your ISMS and making sure it's fully aligned with your business goals.
H3: People Controls
At the end of the day, security involves people. This theme and its eight controls focus on the "human firewall" and address the risks that come with employees, contractors, and anyone else with access to your systems. It covers their entire journey with you, from hiring to departure.
The goal here is simple: reduce the chance of human error, which is still one of the biggest causes of security breaches. When implemented well, these controls help build a strong, security-first culture.
Common controls you’ll see are:
- Security Awareness, Education, and Training: This means running regular training sessions to ensure everyone understands their security duties and can spot threats like phishing emails.
- Remote Working: With so many teams working from anywhere, this control ensures you have clear policies and the right tech to secure information accessed outside the office.
- Screening: For roles with access to sensitive information, this involves doing background checks that are appropriate for the level of risk involved.
H3: Physical Controls
This theme's 14 controls are all about protecting your physical spaces and hardware. It covers everything from securing your office building to protecting individual laptops and servers. It’s easy to forget in our digital-first world, but a lot of our most critical data still lives on equipment in a physical room somewhere.
The need for this kind of structured approach is growing. With over 70,000 certificates expected globally by 2025, Annex A provides a vital blueprint. This is especially critical when you consider that 43% of cyber attacks hit small and medium-sized businesses, often costing them over $200,000 per incident. The demand is fueling a projected 14.2% CAGR for the ISO certification market through 2032.
Key physical controls include:
- Secure Areas: This means using physical entry controls—like key cards, fobs, or biometrics—to protect sensitive locations like server rooms or data centers.
- Security of Equipment and Assets Off-Premises: This control ensures that company gear used off-site, like laptops for remote staff, is properly protected from theft or damage.
H3: Technological Controls
Finally, we get to the tech. This theme contains 34 controls that cover the technology used to protect your information. This is what most people immediately think of when they hear "cybersecurity"—things like firewalls, encryption, and user access rights. These controls are the technical workhorses of your ISMS.
These are the measures you implement across your networks, systems, and applications to enforce your security policies. If you're looking for a practical starting point, our guide on creating an effective access control policy is a great resource.
Examples of crucial technological controls include:
- Access Control: This is the principle of least privilege in action. It's about making sure people only have access to the specific information and systems they absolutely need to do their jobs, and nothing more.
- Cryptography: This control requires you to use encryption to protect the confidentiality and integrity of your sensitive data, both when it's being stored (at rest) and when it's being sent over a network (in transit).
- Secure Coding: If your company develops its own software, this control is about building security in from the start, applying principles that reduce vulnerabilities in your applications.
Now, let's look at how these four themes apply across a typical business. It’s not just an IT problem; security is everyone’s responsibility.
H3: Mapping Annex A Control Themes to Business Functions
The table below gives a few concrete examples of how different departments would be involved in implementing controls from each of the four themes.
| Annex A Theme | Example Control | Applied in HR | Applied in IT | Applied in Facilities |
|---|---|---|---|---|
| Organizational | Supplier Security Policy | Vetting contractors | Reviewing vendor SOC 2 reports | Screening cleaning/security staff |
| People | Security Awareness Training | Conducting onboarding security sessions | Running phishing simulations | Training staff on visitor policy |
| Physical | Secure Areas | Restricting access to personnel files | Managing data center access | Installing and monitoring CCTV |
| Technological | Access Control | Defining role-based permissions | Implementing MFA and password policies | Managing keycard access systems |
As you can see, a strong ISMS requires collaboration across the entire organization to be truly effective.
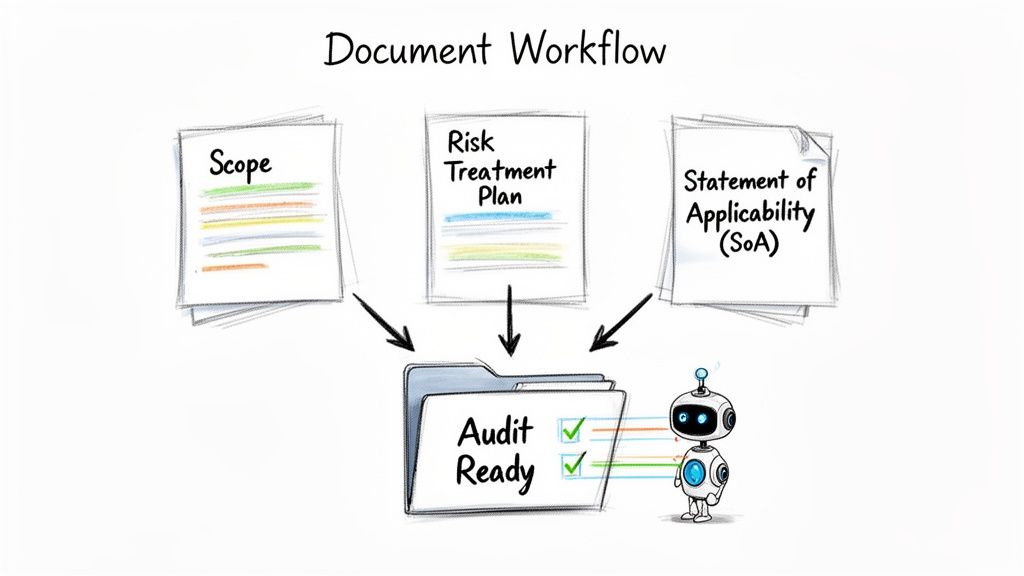
The most important document you'll create related to Annex A is the Statement of Applicability (SoA). This is a mandatory document where you list all 93 controls and, for each one, state if it's applicable, justify your decision to include or exclude it, and note its implementation status. Your SoA is the central roadmap for your security controls and a key piece of evidence for your auditor.
Mastering Documentation and Evidence Collection
There’s an old saying among auditors: "If it isn't documented, it didn't happen." This is the simple, hard truth of ISO 27001. You can have the best security controls in the world, but without the paperwork to prove it, you won't get certified. This is where many teams get bogged down, lost in a maze of policies, procedures, and log files.
Your Information Security Management System (ISMS) needs to be built on a solid foundation of clear, organized, and up-to-date documentation. This isn't just bureaucracy; it's the tangible proof that your security program works exactly as you say it does.
The Mandatory Paper Trail
While you’ll end up with a fair amount of documentation, a handful of documents are absolutely non-negotiable. An auditor will ask for these first, as they set the stage for your entire security program.
Think of them as the constitution of your ISMS:
- ISMS Scope Document: This is where you draw the line in the sand, clearly stating which departments, locations, assets, and processes are covered by your ISMS.
- Information Security Policy: Your company’s high-level commitment to security, signed and endorsed by top leadership.
- Risk Assessment and Risk Treatment Process: A detailed breakdown of your methodology—how you find, analyze, and decide how to handle information security risks.
- Statement of Applicability (SoA): This is the master list. It covers all 93 Annex A controls and justifies why you've included or excluded each one based on your risk assessment.
Beyond these core documents, you'll also need to show evidence of things like competence and awareness training, reports from internal audits, minutes from management review meetings, and logs of any corrective actions taken. You're essentially building a case file to defend your compliance.
The point of documentation isn't to create red tape. It’s to build a clear, repeatable, and verifiable system that proves your commitment to security. A well-documented ISMS should be able to run smoothly even if key people leave the company.
From Paperwork to Proof with Modern Tools
Trying to collect and organize all this evidence by hand is a massive undertaking. I’ve seen compliance managers spend hundreds of hours just trying to connect a specific sentence in a policy document to the right ISO requirement. It’s slow, stressful, and incredibly easy to make a mistake.
This is where modern Governance, Risk, and Compliance (GRC) platforms, especially those with AI, completely change the dynamic. Instead of painstakingly mapping everything manually, you can automate the most grueling parts of evidence collection.
This visual shows a simplified version of that modern workflow, where key documents are analyzed and organized into an audit-ready state.
This automation instantly shows you where your documentation is strong and, more importantly, where you have gaps. This lets your team jump straight to fixing problems instead of spending weeks just trying to find them. If you're just getting started, it's always a good idea to figure out how to conduct a gap analysis to see where you stand.
A Smarter Workflow for Evidence Collection
Picture this: you upload all your existing security policies, procedures, and system configurations into a single, secure platform. An AI agent then gets to work, reading and understanding the content of every single document.
This isn't just a simple keyword search. The AI comprehends the intent behind the language, mapping specific paragraphs or sentences directly to the relevant ISO 27001 clauses and Annex A controls. For instance, it can find the exact text in your "Access Control Policy" that satisfies control A.5.15 and automatically link it as evidence.
What you're left with is an organized, audit-ready body of proof, complete with citations and direct links back to your source documents. It turns that mountain of PDFs into a structured, searchable evidence locker—solving one of the biggest headaches compliance managers have to deal with.
Your Actionable ISO 27001 Audit Checklist
Getting ready for your ISO 27001 audit can feel a lot like cramming for a final exam. But with the right checklist, it transforms from a frantic scramble into a structured, manageable process.
A successful audit isn’t about having a shelf full of dusty binders. It’s about proving your Information Security Management System (ISMS) is a living, breathing part of how your company actually works. This checklist breaks that journey down into four clear phases. If you tackle them one by one, you’ll build a solid body of evidence that not only proves you meet the requirements but also shows just how mature your security program has become.
Let's walk through what you need to do and the exact proof auditors will be looking for.
Phase 1: Scoping and Gap Analysis
This is all about drawing the lines and figuring out where you stand today. Honestly, a fuzzy or poorly defined scope is one of the fastest ways to fail an audit, so getting this right is non-negotiable. You have to be crystal clear about which parts of the business, which services, and what physical locations are covered by your ISMS.
Once the scope is locked in, a gap analysis shows you exactly how much ground you need to cover to meet the standard.
- Define and Document the ISMS Scope: Get this written down in a formal scope statement and, crucially, get management to sign off on it.
- Identify Interested Parties and Their Requirements: Make a list of everyone who has a stake in your information security—customers, employees, regulators, partners—and document what they expect from you.
- Conduct a Gap Analysis Against Clauses 4-10: Go through the mandatory clauses of the standard, one by one, and map them against what you’re doing today. Be honest about where you fall short.
- Review Existing Policies Against Annex A: Take your current security controls and compare them to the 93 controls in Annex A. This will immediately highlight your biggest gaps.
Evidence Auditors Expect: A signed ISMS Scope document, a register of interested parties and their requirements, and a completed gap analysis report that details what you found and how you plan to fix it.
Phase 2: Risk Assessment and Treatment
This is the real heart of your ISMS. From here on out, every single thing you do needs to be justified by the risks you’ve identified. A superficial risk assessment is a massive red flag for an auditor; it signals that your entire security program might just be guesswork.
Your Risk Treatment Plan is arguably the most critical piece of evidence in your entire audit. It’s the strategic document that connects your identified threats directly to the security controls you’ve chosen to implement, proving that your security program is both intentional and comprehensive.
The goal here is to build a logical, defensible story that explains why you’re focusing your efforts on specific security measures.
- Document Your Risk Assessment Methodology: Write down the exact process you use to find, analyze, and evaluate risks. Make it repeatable.
- Create a Risk Register: This is your master list of all identified information security risks. It should include owners, impact scores, and the likelihood of each risk occurring.
- Develop the Risk Treatment Plan: For every significant risk, you need to document your decision: will you mitigate it, accept it, avoid it, or transfer it?
- Produce the Statement of Applicability (SoA): This is the definitive list of all 93 Annex A controls. For each one, you must justify why you've included or excluded it, tying that decision back to your risk assessment.
Evidence Auditors Expect: Your documented risk assessment methodology, a complete risk register, a detailed Risk Treatment Plan, and a finalized Statement of Applicability (SoA).
Phase 3: Control Implementation and Documentation
You’ve got the plan, now it’s time to execute. This phase is about turning the decisions in your Risk Treatment Plan into real-world security controls and documented procedures. You're actively closing the gaps you found earlier by creating the policies, processes, and technical setups required to meet the ISO 27001 requirements.
Just remember the auditor’s mantra: if it isn’t written down, it didn’t happen.
- Implement Necessary Annex A Controls: Roll out the technical, physical, people, and organizational controls you committed to in your SoA.
- Develop Supporting Documentation: Write and get approval for all the required policies and procedures, like your Access Control Policy or Incident Response Plan.
- Conduct Security Awareness Training: Train every single employee on the new security policies and what their personal responsibilities are.
- Collect Evidence of Control Operation: This is huge. You need to gather logs, reports, and records that prove your controls are actually working as intended day-to-day.
Evidence Auditors Expect: Approved policy documents, training records showing who attended, screenshots of system configurations, and operational logs (like records of access reviews or firewall rule changes).
Phase 4: Internal Audit and Management Review
Before the external auditors show up, you need to audit yourself. This final phase isn’t just about finding problems; it’s about demonstrating your commitment to continual improvement, which is a core concept in ISO 27001. Think of the internal audit as a full dress rehearsal. It’s your chance to find nonconformities and fix them before the main event.
The management review then closes the loop, proving that senior leadership is actively involved and invested in the ISMS's performance.
- Conduct a Full Internal Audit: Have an impartial party perform a complete audit of your ISMS against all the standard's requirements.
- Log and Remediate Nonconformities: Document every finding from your internal audit in a log and track the corrective actions until they are fully resolved.
- Hold a Formal Management Review Meeting: Present the performance of the ISMS, the internal audit results, and the current risk picture to top management.
- Document Management Review Outcomes: Keep detailed minutes of the meeting, including any decisions that were made and any resources that were allocated for improvements.
Evidence Auditors Expect: A complete internal audit report, a log of nonconformities and their corrective actions, and the signed minutes from your management review meeting.
Common Questions About ISO 27001 Requirements
When you start digging into ISO 27001, you’ll naturally run into some practical questions. Getting a handle on these key concepts early on can save you a ton of headaches down the road. Let's walk through some of the most common queries we hear from teams on their certification journey.
What Is the Difference Between ISO 27001 Requirements and Annex A Controls?
This is probably the most crucial distinction to get right. It’s easy to get them tangled up, but they serve two very different purposes.
Think of the main ISO 27001 requirements—found in Clauses 4 through 10—as the blueprint for your security program. They are the mandatory instructions telling you that you must build and run a formal Information Security Management System (ISMS). These clauses are all about the 'what' and 'why'—establishing context, getting leadership on board, planning, and continuous improvement.
Annex A, on the other hand, is your toolbox. It’s a reference list of 93 potential security controls you can choose from to build out that program. Annex A provides the 'how'. It’s not a checklist you have to complete; it’s a menu of options to help you address the specific risks you’ve identified.
The bridge connecting the blueprint and the toolbox is your risk assessment. That process tells you exactly which tools from Annex A you need to pull out to manage your organization's unique security risks.
Do We Have to Implement All 93 Annex A Controls?
No, and believing you have to is one of the most common and costly mistakes. This misconception leads teams down a rabbit hole of unnecessary work. ISO 27001 is designed to be flexible and risk-based, not a one-size-fits-all mandate.
Your security measures should be directly proportional to the threats you face.
To manage this, you'll create a critical document called the Statement of Applicability (SoA). The SoA is essentially your inventory sheet, listing all 93 Annex A controls. For every single control, you must document whether you've implemented it and—this is the important part—justify your decision.
If a control isn't relevant to your risks, you can absolutely exclude it. For instance, a cloud-native company with no physical office could easily justify excluding controls related to physical site security. The key is that every decision to include or exclude a control must be backed by a clear, logical reason documented in your SoA.
How Can AI Tools Accelerate Our ISO 27001 Compliance Process?
Getting ready for an ISO 27001 audit traditionally involves a mountain of manual labor. Teams spend hundreds of hours digging through documents, policies, and system settings just to find the evidence needed to prove they meet each requirement. It's tedious and incredibly easy to miss something.
This is where modern AI tools are a game-changer. An AI-powered platform can ingest all of your GRC documentation at once—policies, procedures, reports, everything. It reads and understands the content, then automatically maps specific phrases and paragraphs to the corresponding ISO 27001 clauses and Annex A controls.
This instantly shows you where you're covered and, more importantly, where the gaps are. It all but eliminates human error in the evidence-gathering phase, creates a clean audit trail, and frees up your team to focus on fixing problems instead of hunting for paperwork. It makes the path to certification much faster and far more reliable.
What Are the Most Common Audit Nonconformities?
Auditors see the same mistakes over and over again. If you know what they're looking for, you can get ahead of the game and strengthen your weakest points before the audit even begins.
Here are some of the most frequent reasons for a nonconformity:
- An Incomplete Statement of Applicability (SoA): The most common pitfall is excluding controls without a well-documented, risk-based reason.
- A Weak Risk Assessment: Auditors will dig into your risk assessment process. If it isn't thorough or fails to identify obvious risks, it's an immediate red flag.
- Poor Evidence of Management Review: A lack of detailed meeting minutes and clear action items tells an auditor that leadership isn't truly engaged in the ISMS (a direct violation of Clause 9.3).
- Gaps in Security Awareness Training: Many organizations can't prove that their employees have been properly trained or that they understand their security duties (Clauses 7.2 & 7.3).
- Missing Documented Procedures: Clause 8 requires many key operational processes to be formally documented. If the procedure isn't written down, as far as an auditor is concerned, it doesn't exist.
By focusing your internal reviews on these common trouble spots, you can fix the issues that auditors are most likely to find.
Stop wasting weeks manually mapping evidence. At AI Gap Analysis, our platform ingests your documents and instantly maps your content to ISO 27001 requirements, showing you exactly where you stand in minutes, not months. Start your audit preparation with confidence at https://ai-gap-analysis.com.