February 5, 2026
cloud computing securitycloud security challengescloud risk managementISO 27001cloud compliance
Navigating Security Challenges in Cloud Computing
Uncover the top security challenges in cloud computing and learn practical mitigation strategies to protect your data, manage risk, and ensure compliance.
21 min readAI Gap Analysis

When businesses jump into the cloud, they often find the security landscape is a lot different than what they're used to. The biggest hurdles usually come down to a few key things: getting configurations wrong, shaky access controls, and not fully grasping the shared responsibility model. The problem is that cloud adoption moves at lightning speed, while security often struggles to keep up, opening the door to data breaches, compliance nightmares, and even insider threats.
The Escalating Threat Landscape in Cloud Computing
Moving to the cloud has been a game-changer, giving companies incredible flexibility and the power to scale on demand. But this gold rush to the cloud has also created a new, and often confusing, frontier for security. What used to be a technical checklist is now a core business function.
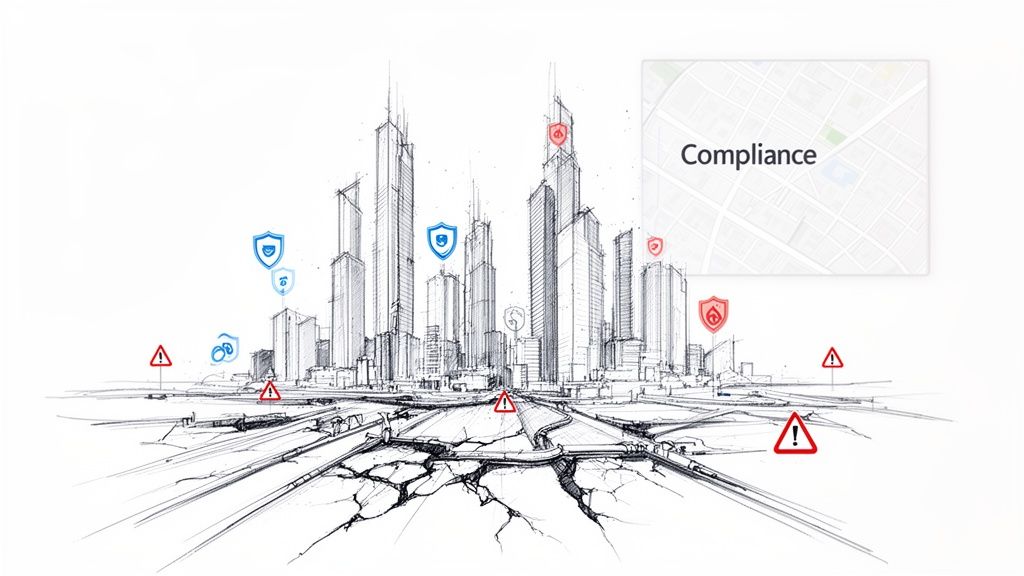
Think of it this way: your business is building a high-tech city in the clouds. New skyscrapers—your apps and services—go up almost overnight. But the underlying infrastructure, like the roads, power grids, and emergency services (your security controls), can't always keep pace. This gap between rapid growth and solid security creates hidden vulnerabilities that are tough to spot and even harder to fix.
The fallout from these gaps is pretty shocking. The latest numbers show that 98% of companies have had a cloud breach in the past couple of years, and a staggering 43% have dealt with 10 or more separate incidents. These aren't small hiccups, either. A single breach from a simple misconfiguration costs, on average, a whopping $3.86 million. To make matters worse, it takes most companies about 251 days just to find and contain the problem. For a deeper dive, you can explore more cloud security statistics to see the full picture.
Navigating the Key Challenges
This guide is your map for navigating this tricky terrain. We're going to break down the biggest security challenges you'll face in the cloud, skipping the dense technical jargon to give you practical advice you can actually use.
We’ll focus on the big-ticket items:
- The Shared Responsibility Model: Figuring out exactly where your cloud provider’s job ends and yours begins.
- Common Misconfigurations: Pinpointing the small, everyday mistakes that cause the most damage.
- Identity and Access Management (IAM): Mastering who gets access to what, which is the bedrock of any solid cloud defense.
- Data Protection and Compliance: Making sure your data stays safe and you're ticking all the right boxes for regulations like ISO 27001.
When we frame these challenges correctly, compliance frameworks stop feeling like a bureaucratic chore and become a survival guide. A smart security plan doesn't just stop attacks; it builds a solid foundation for growth and earns customer trust in a world where everything is connected.
To help you get a quick overview, here's a snapshot of the challenges we'll be discussing.
Key Cloud Security Challenges at a Glance
| Challenge | Primary Risk Area | Common Business Impact |
|---|---|---|
| Shared Responsibility | Governance & Operations | Misaligned security efforts, leading to critical gaps and finger-pointing. |
| Misconfigurations | Infrastructure Security | Accidental data exposure, unauthorized access, and compliance violations. |
| IAM | Access Control | Over-privileged accounts, insider threats, and compromised credentials. |
| Data Protection | Data Security & Privacy | Data breaches, intellectual property theft, and loss of customer trust. |
| Multi-Tenant Risks | Infrastructure Security | Potential for "noisy neighbor" issues or cross-tenant data leakage. |
| Supply Chain | Third-Party Risk | Vulnerabilities inherited from third-party services or APIs. |
| Compliance & Auditability | Governance & Risk | Fines, legal trouble, and difficulty proving security posture to auditors. |
Throughout this guide, we'll unpack each of these issues, giving you actionable checklists and real-world examples. The goal is simple: to give you and your team the know-how to not only spot risks but to build strong controls that turn your cloud environment from a liability into a secure, resilient asset.
Demystifying the Cloud's Shared Responsibility Model
One of the biggest—and most misunderstood—security hurdles in the cloud is the shared responsibility model. It’s a concept that trips up even seasoned IT teams. Many organizations move to the cloud assuming their provider, whether it's AWS, Azure, or GCP, handles all security. That assumption is a dangerous one, and it's behind a staggering number of cloud data breaches.
Think of it like renting a storage unit at a super-secure facility. The facility owner—your cloud provider—is responsible for the building itself. They provide the reinforced walls, the perimeter fence, the 24/7 guards, and the locks on the main gate. This is the security of the cloud. It covers the physical data centers, the servers, the networking gear, and the core virtualization software.
But you, the renter, are responsible for what happens inside your unit. You decide what to store, you put your own padlock on the door, and you control who gets a copy of the key. This is the security in the cloud, and it’s always on you.
How the Lines Shift with Different Cloud Services
Where that line is drawn depends entirely on the type of cloud service you’re using: Infrastructure-as-a-Service (IaaS), Platform-as-a-Service (PaaS), or Software-as-a-Service (SaaS). As you move from IaaS to SaaS, the cloud provider shoulders more of the burden, but your responsibility for your data never vanishes completely.
The provider secures the container, but you hold the key to your data within it.
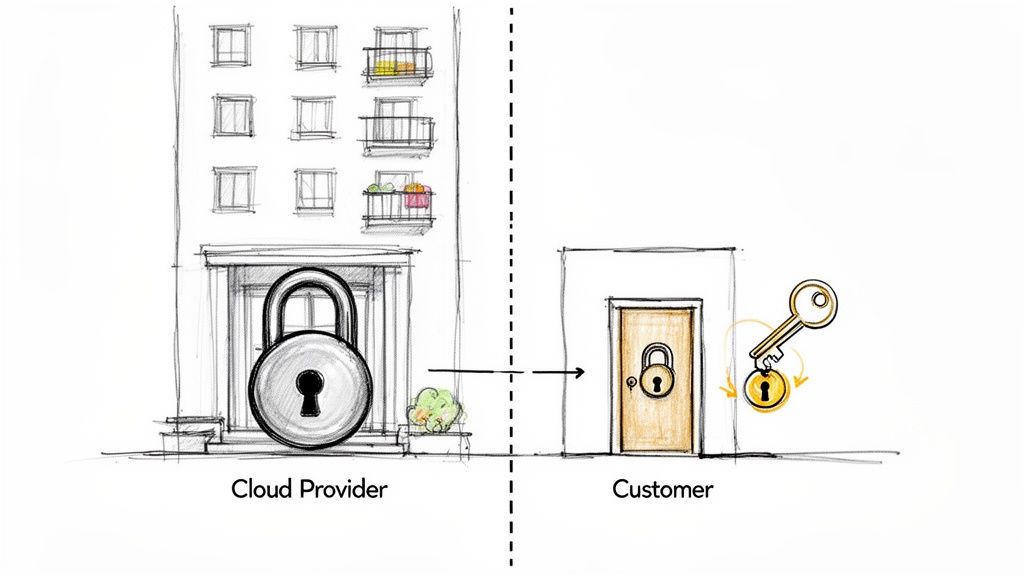
The critical takeaway is this: no matter how much the provider manages, you are always accountable for securing your data, managing who can access it, and protecting your endpoints.
Let's break it down by service model:
-
Infrastructure-as-a-Service (IaaS): This is the "DIY" model. It gives you the most control but also hands you the most responsibility. The provider handles the raw infrastructure, but you’re in charge of securing everything from the operating system up—network settings, applications, and all your data. It’s like leasing an empty commercial space; you have to build out the interior and install your own security system.
-
Platform-as-a-Service (PaaS): Here, the provider takes care of the infrastructure and the underlying operating system and runtime environment. You just focus on securing the applications you build and the data they handle. Think of it as renting a fully equipped professional kitchen. The ovens and plumbing are maintained for you, but you're responsible for your recipes and locking the door when you leave.
-
Software-as-a-Service (SaaS): With SaaS, the provider manages almost everything, right down to the application itself. Your job narrows significantly, but it’s still crucial: you manage user access and are responsible for securing the data you pump into the service. This is like using an armored car service. They provide the secure transport, but you’re still responsible for what you put in the lockbox and who you send it to.
No matter which cloud model you choose, your organization is always on the hook for data classification, governance, and user access. A cloud provider will never be liable for a data breach caused by your team leaving a storage bucket public or enforcing weak password policies.
Getting this division of labor right is the absolute foundation of a solid cloud security program. It eliminates the deadly "I thought you were handling that" scenario that attackers love to exploit. This isn't just a best practice; it's a non-negotiable for staying compliant and keeping your data safe.
Breaking Down the Biggest Threats to Your Cloud Security
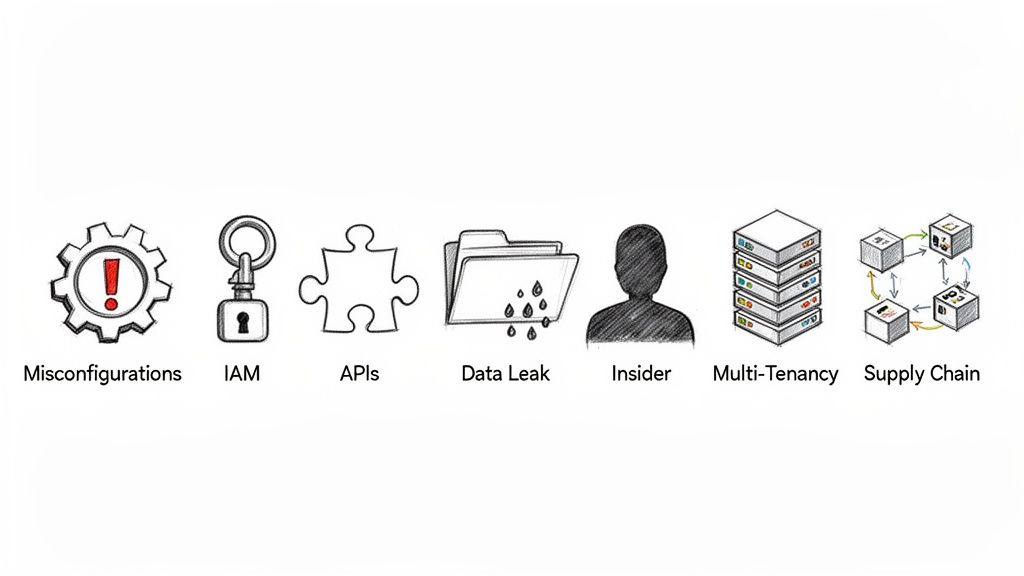
Knowing the shared responsibility model is step one. Now, it's time to dig into the actual threats that slip through the cracks of that model. These aren't just theoretical risks; they're the real-world problems security teams wrestle with every single day. Each one is a different angle an attacker can use to turn a tiny oversight into a full-blown incident.
Let's get practical and break down the seven most pressing security challenges in cloud computing that businesses are up against. We'll look at what causes them, the kind of damage they do, and how you can start building a solid defense.
1. Cloud Misconfigurations
Imagine you've built a high-tech vault but left a side door unlocked by mistake. That’s a cloud misconfiguration. It’s not a weakness in your cloud provider’s security; it's a simple, human error in how you’ve set up your own resources.
Human error is, by far, the biggest culprit here. A staggering 88% of all data breaches are caused by human mistakes, and cloud misconfigurations are a huge piece of that pie. In 2024 alone, these setup errors were behind 23% of all cloud security incidents, and about 27% of companies got hit with a public cloud breach because of them. Common examples are botched Identity and Access Management (IAM) rules, exposed API keys, or just forgetting to turn on encryption for a storage bucket. You can find more eye-opening cloud computing statistics that paint the full picture.
- Root Cause: The cloud moves fast—often too fast for manual checks. A developer might spin up a temporary database for a quick test and forget to lock it down, or a sysadmin might use overly permissive network rules to get something working quickly.
- Real-World Impact: Back in 2019, a major financial firm exposed the personal data of over 100 million customers. The cause? A misconfigured web application firewall. One mistake opened the door for an attacker, leading to devastating financial and reputational costs.
2. Flawed Identity and Access Management
Identity and Access Management (IAM) is basically the bouncer for your cloud environment. It’s what decides who gets in, where they can go, and what they’re allowed to touch. When your IAM is flawed, it's like handing out master keys to the entire building instead of giving people keys only to the offices they need to be in.
The goal should always be least privilege access, which is a simple idea: give people the absolute minimum permissions they need to do their job, and nothing more. But in the real world, for the sake of convenience, we often grant way too much access. This creates a massive attack surface. If a hacker gets control of an account with oversized permissions, they can wander through your cloud environment like they own the place.
Think of it this way: a junior marketing team member should have access to the social media scheduling tool, not the production database containing customer financial records. Flawed IAM blurs these lines, putting critical assets at unnecessary risk.
Getting IAM right is non-negotiable for a strong cloud defense. It’s not just about passwords; it's about having a clear, enforceable strategy.
3. Insecure Application Programming Interfaces
Application Programming Interfaces (APIs) are the invisible connections that let cloud services and apps talk to each other. They're the reason your mobile banking app can connect to the bank's servers or your favorite online store can process a payment. But because they are designed to expose data and functions, they're a magnet for attackers.
Insecure APIs have a few common weak spots:
- Weak Authentication: Letting requests through without properly checking who they're from.
- No Rate Limiting: Allowing an attacker to bombard the system with thousands of requests a second to overload it or guess passwords.
- Excessive Data Exposure: Sending back more information than is actually needed, like internal user IDs or other sensitive tidbits.
The fundamental issue is that APIs are often treated like internal plumbing, not as public-facing doors that need deadbolts. A hacker who finds a vulnerable API can often bypass all your other security layers to get straight to your data.
4. Data Breaches and Leakage
While misconfigurations and bad IAM are the "how," a data breach is the painful result. A data breach is simply when someone unauthorized gets their hands on sensitive or confidential information. In the cloud, this can happen in a hundred different ways, from an unsecured storage bucket to a clever phishing email that tricks an admin into giving up their login details.
Data leakage is its sneakier cousin. This is the accidental exposure of data, often by employees who mean no harm. For example, someone might accidentally share a link to a sensitive cloud document with an outsider, or a developer might mistakenly commit secret keys to a public code repository.
Stopping breaches and leaks isn't about one magic tool. It's about layers of defense:
- Data Encryption: Scrambling your data so it's unreadable, both when it's just sitting in storage (at rest) and when it's moving across the network (in transit).
- Data Loss Prevention (DLP) Tools: These systems can automatically spot sensitive information and block it from being shared where it shouldn't be.
- Regular Audits: Proactively and constantly scanning your environment for exposed data or insecure settings.
5. Insider Threats and Account Hijacking
Not every threat is a shadowy hacker from across the globe. An insider threat comes from someone who already has legitimate access—a current or former employee, a contractor, or even a business partner. Sometimes it's malicious, like a disgruntled employee deleting critical files. Other times, it's completely accidental, like an employee falling for a phishing scam.
Account hijacking is a direct consequence of this. A bad actor steals a real user's login details, often through phishing or malware, and then waltzes into your systems pretending to be them. To your security tools, everything looks normal because the attacker is using a trusted identity. This is precisely why just having a password isn't enough anymore.
6. Multi-Tenancy Vulnerabilities
One of the reasons the public cloud is so affordable is multi-tenancy. It means that you and many other customers (or "tenants") are sharing the same physical hardware—the same servers, storage drives, and network gear. Your data and applications are kept separate through software.
Think of it like an apartment building. You have your own locked apartment, but you share the building’s foundation, plumbing, and wiring with all your neighbors. Cloud providers are incredibly good at building strong walls between tenants, but the tiny, theoretical risk of a "noisy neighbor" or a crack in the foundation is one of the more complex security challenges in cloud computing.
While a direct attack from one tenant to another is extremely rare thanks to the providers' advanced security, a more practical concern is resource competition. A "noisy neighbor" could hog resources like CPU or network bandwidth, slowing down performance for everyone else on that same piece of hardware.
7. Supply Chain Attacks
Your cloud security is only as strong as its weakest link. Very often, that weak link isn't something you built—it's a third-party vendor or an open-source library your developers use. A supply chain attack goes after these less-secure components to ultimately compromise your system.
Here’s a classic example: an attacker sneaks malicious code into a popular open-source software package that thousands of developers rely on. When your team includes that package in your application, the hidden malicious code comes right along with it, creating a backdoor into your cloud environment.
This kind of attack is especially nasty because it sidesteps your direct defenses. You can have a perfectly configured firewall and the best monitoring tools, but you still inherit the vulnerabilities of every third-party tool you depend on. The only way to fight this is with strict vendor security reviews and tools that can scan your code for vulnerabilities hidden inside the components you use.
Putting Practical Mitigation Strategies into Action
Knowing the security challenges in the cloud is one thing, but actually defending against them is a whole different ballgame. To move from theory to practice, you need a deliberate, multi-layered approach. It's not about finding a single silver bullet; it's about building a robust security system where every part supports the others.
This mindset shifts you away from just reacting to problems and toward proactive controls that shrink your attack surface from the very beginning. Think of it like setting up a comprehensive security system for your home—you need strong locks on the doors, a reliable alarm, and clear rules about who gets a key. Each piece plays a critical, distinct role.
The goal is to build a security posture that's both tough and flexible enough to keep up with the fast-paced nature of cloud environments. Let's break down the essential tactics your team can start using today.
Automate and Enforce Your Security Posture
Manual security checks just can’t keep up with the speed and scale of the cloud. The first and most important step is to automate how you monitor and enforce your security policies. This is where Cloud Security Posture Management (CSPM) tools become absolutely essential.
Think of a CSPM tool as a tireless security guard that's always on duty. It constantly scans your cloud environments for common misconfigurations, like public S3 buckets or network rules that are far too permissive. When it finds something that deviates from your security baseline, it can often fix it on the spot, closing security holes before anyone has a chance to exploit them.
This proactive stance is a game-changer. By automating detection, you transform security from a once-in-a-while, checklist-based task into a continuous, vigilant process that moves at the speed of your development teams.
Fortify Identity and Access Management
In the cloud, identity has become the new perimeter, and locking it down is non-negotiable. A shocking number of cloud breaches start with weak or poorly managed credentials. A strong Identity and Access Management (IAM) strategy is the foundation for stopping this.
Your IAM defense should be built on two core principles:
- Multi-Factor Authentication (MFA): Make MFA mandatory for all users, especially anyone with admin-level access. In today’s world, a password alone is simply not enough to stop phishing and credential-stuffing attacks.
- Zero-Trust and Least Privilege: Work from a "never trust, always verify" mindset. Grant users and services only the bare minimum level of access they need to do their jobs. This one move drastically limits an attacker's ability to move around your network if they do manage to compromise an account.
A common mistake we see is people granting broad, standing permissions just for convenience. A zero-trust model flips that on its head. It demands verification for every single access request and treats every user and device as a potential threat until proven otherwise.
Proactively Hunt for Weaknesses
You can't afford to just sit back and wait for attackers to find your vulnerabilities. You have to find them first. Proactive testing is crucial for discovering and fixing weaknesses before they turn into a full-blown crisis. This means using a mix of automated scanning and manual, expert-led assessments.
Make these activities a regular part of your routine:
- Vulnerability Scanning: Continuously scan all your cloud assets—from virtual machines and containers to the applications themselves—for known software vulnerabilities and missing patches.
- Penetration Testing: Bring in ethical hackers to simulate real-world attacks on your cloud infrastructure. Their findings give you an invaluable, unbiased look at how resilient your security truly is.
This offensive approach helps you see your environment through an attacker's eyes, uncovering blind spots that your automated tools might have missed.
Implement End-to-End Data Encryption
Finally, you have to assume that a breach will happen sooner or later and protect your data with that reality in mind. Data encryption is your last line of defense, making stolen data completely useless to anyone who shouldn't have it. It’s vital to encrypt data at every single stage.
- Data at Rest: Encrypt everything stored in your databases, object storage like S3, and on virtual machine disks.
- Data in Transit: Use strong TLS/SSL protocols to encrypt data as it moves between your services or across the public internet.
A well-rehearsed incident response plan is the final piece of the puzzle. Imagine a CSPM alert fires, flagging an unusual API call from a developer's account. Because you have a plan, an automated workflow immediately kicks in, temporarily suspending the account, isolating the affected resources, and notifying the on-call engineer—all within minutes. This turns a potential catastrophe into a controlled, low-impact event. For those getting ready for formal audits, understanding how these strategies align with compliance is key, and you can learn more by streamlining cloud security assessments in our detailed guide.
Aligning Cloud Security With ISO 27001 Compliance
Tackling the security challenges of cloud computing isn't just a technical necessity—it's the foundation for achieving and keeping formal certifications like ISO 27001. Don't think of ISO 27001 as a separate, bureaucratic headache. Instead, view it as a structured blueprint for building the very defenses we've been discussing.
Every single mitigation strategy, from tightening up access controls to encrypting sensitive data, maps directly to a specific requirement within the ISO 27001 framework. This natural alignment transforms your security work into tangible proof for auditors and stakeholders, showcasing a mature and forward-thinking approach to managing risk.
Bridging the Gap Between Cloud Risks and ISO Controls
The real magic happens when you connect your practical, day-to-day cloud security measures to the specific Annex A controls of ISO 27001. For instance, all that effort you put into securing user identities isn't just good practice; it's how you directly satisfy control A.9.2 (User access management).
Let's look at a few more examples of how this works:
- Data Breach Risks: These are covered squarely by A.18.1.5 (Use of cryptography), which calls for encrypting data both when it's stored (at rest) and when it's moving (in transit).
- Misconfiguration Gaps: Controls like A.12.1.2 (Protection against malware) and A.14.2.1 (Secure development policy) provide the framework for setting up secure baselines and automated checks to catch errors.
- API Vulnerabilities: These fall under A.14.2.5 (Secure system engineering principles), pushing teams to build security into the entire application lifecycle from the very beginning.
This proactive approach—integrating automation, enforcement, and continuous testing—is what a mature cloud defense strategy looks like in action.
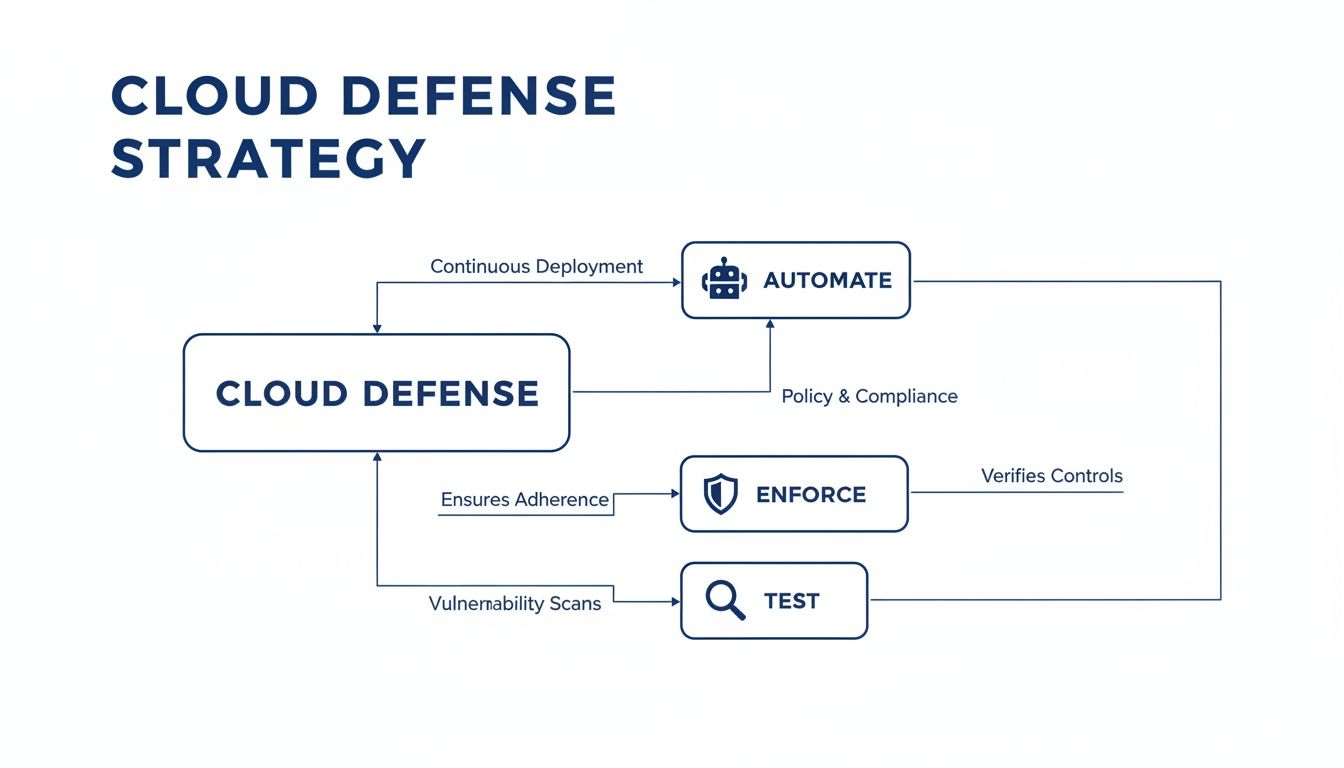
As you can see, strong security isn't a one-and-done task. It's a continuous cycle where automated tools enforce your security policies and regular testing confirms they're actually working as intended.
Turning Security Actions Into Audit-Ready Evidence
The speed of modern threats has opened up a major detection gap. The latest data is pretty sobering: 66% of cybersecurity experts admit they don't have strong confidence in their ability to respond to cloud threats in real time. Access-related weaknesses are a massive contributor to this problem, playing a role in 83% of cloud security breaches as attackers use automation to find misconfigurations faster than any human team can. You can find more details on this growing cloud security gap on DRJ.com.
This is where tying your work to a framework like ISO 27001 really pays off. The standard requires you to document your controls, creating a clear audit trail that proves your security measures are not only in place but also effective and consistently monitored.
When you look at your security work through a compliance lens, every action you take helps build your evidence locker. For any organization working toward certification, our guide offers a deeper dive into what ISO 27001 compliance entails. This strategic mindset shifts compliance from being a final hurdle to being the natural outcome of a well-executed security program.
Automating Audits with AI-Powered Gap Analysis
Let's be honest: traditional compliance audits are a massive headache for any security team. They’re a grind of manual, time-consuming tasks that are easily derailed by human error. This is especially true in the cloud, where evidence is scattered and configurations change daily. The old way feels like a painful, backward-looking exercise in chasing paperwork.
Picture a compliance manager, Sarah, gearing up for an ISO 27001 audit. In the past, this meant weeks of hunting through shared drives, bugging engineers for system reports, and manually matching hundreds of policy documents against the standard’s dense requirements. It was an exhausting marathon of finding, organizing, and justifying evidence.
This year, her team tries a different approach. Instead of the usual manual slog, Sarah uses an AI-powered gap analysis platform. The entire dynamic of the audit process shifts, turning a reactive scramble into a proactive, strategic activity.
How an AI-Driven Approach Works
Getting started is surprisingly simple. Sarah uploads all of her company’s security documentation into the secure platform—this includes everything from policies and procedures to cloud configuration reports and vulnerability scans. The AI gets to work immediately.
Within minutes, it's analyzing every document and connecting the dots between her company's existing controls and the specific clauses of ISO 27001. The platform doesn't just match keywords; it actually understands the context and intent behind the documents.
This screenshot shows how an AI tool can analyze uploaded documents to find evidence for a specific compliance requirement.
The real magic is its ability to generate audit-ready findings with direct citations. It links every answer back to the exact page and section in the source material, so verification is instant.
The output is a comprehensive, audit-ready report delivered in a fraction of the time. The report pinpoints exactly where the gaps are, lays out clear recommendations for fixing them, and provides verifiable, evidence-linked answers for every control. Sarah can now focus her team's energy on closing actual security gaps rather than drowning in administrative work. If you're curious about how this technology is changing the game, you can learn more about the role of AI for regulatory compliance in our detailed article.
This shift from manual evidence collection to automated analysis is critical for managing the security challenges in cloud computing. It helps teams keep up with dynamic environments and turns compliance from a dreaded annual event into a continuous, data-driven process.
By letting technology handle the heavy lifting of finding and drafting evidence, teams can maintain a state of continuous compliance. Audit preparation becomes less of a fire drill and more of a routine check-in, freeing up your experts to do what they do best: strengthening security.
Quick Answers to Common Cloud Security Questions
We get a lot of questions about navigating cloud security. Here are some of the most common ones, answered straight from our experience.
What’s the Single Biggest Cloud Security Risk for a Small Business?
Honestly? It's often the simple stuff: Identity and Access Management (IAM) and basic misconfigurations.
Many small businesses accidentally give employees far more access than they actually need. It’s also incredibly common to see an unsecured storage bucket left open to the internet. These aren’t sophisticated, complex hacks—they’re the digital equivalent of leaving the front door unlocked, making them easy targets for opportunistic attackers.
Does a Multi-Cloud Strategy Make Security Harder?
Yes, it almost always does. When you're juggling multiple cloud providers, you're also juggling different security tools, different configuration rules, and completely separate ways of managing user access.
This fragmentation creates a real headache. You lose a single, clear view of your entire environment, making it nearly impossible to enforce consistent security policies. Before you know it, you have dangerous gaps you can't even see.
Is It Possible to Be 100% Secure in the Cloud?
In a word, no. Aiming for 100% security is a myth.
Think of security less like a destination you can arrive at and more like a continuous process of managing risk. The real goal is to build a resilient system—one that can spot threats early, respond to them effectively, and recover quickly with minimal damage.
Ready to stop chasing compliance paperwork and start focusing on the risks that actually matter? With AI Gap Analysis, you can automate your evidence collection for frameworks like ISO 27001. It turns weeks of manual effort into a fast, accurate, and audit-ready report. See how it works and get back to what you do best.